-


Security
/ 2 weeks agoCISA Warns of Active Exploits Targeting Zimbra, SharePoint Flaws
The U.S. cybersecurity and Infrastructure Security Agency (CISA) has issued an urgent directive for federal agencies to patch two actively exploited...
-


Security
/ 2 weeks agoiOS Exploit Kit Uses 6 Flaws, 3 Zero-Days for Device Takeover
A sophisticated exploit kit targeting Apple iOS devices has been actively used by multiple threat actors to steal sensitive data since...
-

Security
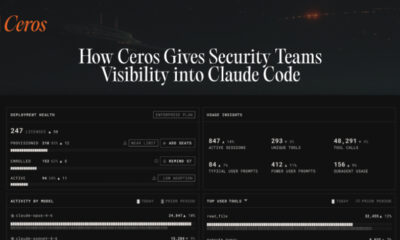
/ 2 weeks agoCeros Provides Security Tools for Claude Code AI Agents
A new security platform has been introduced to manage the access and activities of artificial intelligence coding agents within corporate technology...
-


Security
/ 2 weeks agoNew Android Banking Malware Perseus Targets Notes Apps
cybersecurity researchers have identified a new and sophisticated Android malware family, named Perseus, that is actively being distributed to conduct financial...
-

Security
/ 2 weeks agoCybersecurity Bulletin Details Ransomware, Exploits, and Phishing
A recent <a href="https://delimiter.online/blog/cisco-zero-day-ransomware/” title=”cybersecurity”>cybersecurity bulletin has detailed a series of ongoing threats targeting enterprise networks and software platforms. The report,...
-

Security
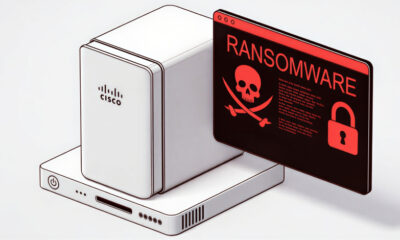
/ 2 weeks agoInterlock Ransomware Uses Cisco Zero-Day for Root Access
A major cybersecurity firm is warning of an active ransomware campaign that is exploiting a critical, recently disclosed vulnerability in Cisco‘s...
-


Security
/ 2 weeks agoUS Sanctions North Korean IT Workers Funding WMD Programs
The United States has imposed sanctions on a network of North Korean information technology professionals and companies accused of infiltrating the...
-


Security
/ 2 weeks agoApple Patches WebKit Flaw Allowing Same-Origin Policy Bypass
Apple has released its first set of security updates for 2026, addressing a critical vulnerability in the WebKit browser engine that...
-


Security
/ 2 weeks agoUbuntu Flaw CVE-2026-3888 Allows Local Attackers Root Access
A significant security vulnerability has been identified in default installations of Ubuntu Desktop, potentially enabling attackers to gain complete control of...
-


Security
/ 2 weeks agoSecurity Teams Struggle to Map Attack Paths to Critical Assets
Security professionals globally are facing a significant challenge in identifying how discrete security issues combine to form dangerous pathways to an...