-


Security
/ 4 weeks agoOsaka Teen Arrested for Hacking 7 Million User Records
A 17 year old was arrested in Osaka, Japan on December 4, 2025, under the country’s Unauthorized Access Prohibition Act. Authorities...
-

Security
/ 4 weeks agoWeekly Security Recap: AI Phishing, Android Spyware, Linux Exploit
A series of significant security vulnerabilities and attack campaigns have been identified this week across multiple platforms, highlighting an accelerating shift...
-


Security
/ 4 weeks agoProgress Patches Critical MOVEit Automation Authentication Bypass Bug
Progress Software has released security updates to address two vulnerabilities in its MOVEit Automation product, including a critical flaw that could...
-

Security
/ 4 weeks agoPhishing Campaign Targets 80 Plus Firms With RMM Tools
A persistent Phishing Campaign that began in at least April 2025 has compromised more than 80 organizations, primarily in the United...
-

Security
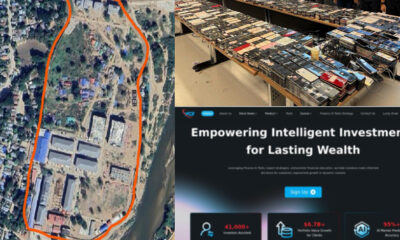
/ 4 weeks agoGlobal Operation Arrests 276, Shuts Down 9 Crypto Scam Centers
An international law enforcement operation, coordinating authorities from the United States and China, has resulted in the arrest of at least...
-


Security
/ 4 weeks agoCISA adds actively exploited Linux root bug to KEV catalog
The United States cybersecurity and Infrastructure Security Agency (CISA) has added a recently disclosed security vulnerability affecting multiple Linux distributions to...
-

Security
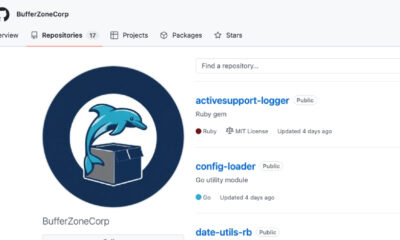
/ 1 month agoNew Supply Chain Attack Uses Ruby Gems And Go Modules
A new software supply chain attack campaign has been observed targeting development infrastructure. Threat actors deployed so called sleeper packages to...
-


Security
/ 1 month agoTwo Cybersecurity Experts Sentenced Over BlackCat Ransomware Role
The United States Department of Justice (DoJ) announced on Thursday that two Cybersecurity professionals have been sentenced to four years each...
-


Security
/ 1 month agoMSPs Lose Cybersecurity Revenue to Five Sales Gaps
The managed security services market is expanding rapidly, projected to grow from $38.31 billion in 2025 to $69.16 billion by 2030,...
-


Security
/ 1 month agoChina-Linked Hackers Target Asian Governments and NATO State
cybersecurity researchers have uncovered a new espionage campaign linked to China, targeting government and defense sectors across South, East, and Southeast...