-
Security
/ 3 weeks agoUnpatched Linux Kernel Flaw Dirty Frag Grants Root Access
Security researchers have disclosed details of a new local privilege escalation vulnerability in the Linux kernel, designated as an unpatched flaw...
-

Security
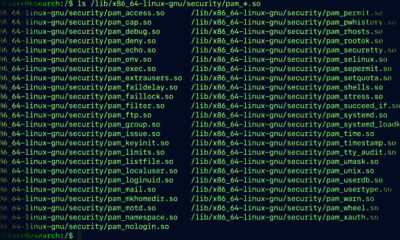
/ 3 weeks agoNew Linux Backdoor PamDOORa Steals SSH Credentials via PAM
A newly identified Linux backdoor, named PamDOORa, is being sold on a Russian-language cybercrime forum for $1,600. The tool allows attackers...
-


Security
/ 3 weeks ago25 Million Alerts Reveal Weakness in Low-Severity Security Threats
A new analysis of over 25 million security alerts from operational enterprise environments has revealed a systemic problem within security operations...
-

Security
/ 3 weeks agoLinux Malware Targets Developer Credentials in Supply Chain Attack
A newly identified Linux malware, known as Quasar Linux RAT (QLNX), is actively targeting software developers to steal credentials and compromise...
-


Security
/ 4 weeks agoIncident Response Gaps Undermine Readiness for Security Teams
Organizations that have secured an incident response retainer or pre-approved a third party firm may still be unprepared for an actual...
-


Security
/ 4 weeks agoSecurity Bulletin Highlights Edge Vulnerabilities and Urgent Patch Alerts
A new weekly security bulletin has detailed a significant volume of cybersecurity incidents, including exposed plaintext passwords in Microsoft Edge, multiple...
-


Security
/ 4 weeks agoPAN-OS RCE exploit under active use enables root access and espionage
A critical remote code execution vulnerability in Palo Alto Networks <a href="https://delimiter.online/blog/CVE-2026-0300-exploitation/” title=”PAN-OS”>PAN-OS software is being actively exploited in the wild,...
-

Security
/ 4 weeks agoOne Click Total Shutdown: Webinar Targets Stealth Breaches
cybersecurity professionals are being forced to reconsider their incident response strategies as attackers increasingly rely on artificial intelligence to initiate stealth...
-


Security
/ 4 weeks agoNew Cloud Credential Theft Framework PCPJack Exploits Five CVEs
cybersecurity researchers have uncovered a new credential theft framework named PCPJack that actively targets exposed cloud infrastructure. The attackers behind this...
-


Security
/ 4 weeks agoIvanti EPMM Vulnerability Exploited in Active Attacks Grants Admin Access
A critical security vulnerability in Ivanti’s Endpoint Manager Mobile (EPMM) software is currently under active exploitation in limited cyberattacks, according to...