-


Security
/ 1 month agoCritical cPanel Authentication Flaw Found, Users Urged to Update
Server administrators and hosting providers using cPanel software are being advised to apply the latest security updates immediately. This follows the...
-


Security
/ 1 month agoExposure Management Platforms: What Most Vendors Miss
Every security team has a version of the same story. The quarter ends with hundreds of vulnerabilities closed. The dashboards are...
-


Security
/ 1 month agoAI Attack Automation Demands Faster Exposure Validation
In February 2026, security researchers documented a significant shift in cyber threat tactics: adversarial groups are now deploying custom artificial intelligence...
-


Security
/ 1 month agoDPRK Hackers Use AI-Designed npm Malware in Supply Chain Attack
cybersecurity researchers have identified malicious code hidden inside an npm package that was generated as a dependency by Anthropic’s Claude Opus...
-

Security
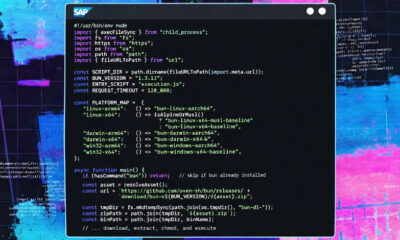
/ 1 month agoSAP npm Packages Hit by Credential Stealing Supply Chain Attack
cybersecurity researchers have identified a new supply chain attack campaign that is targeting SAP related npm packages with malware designed to...
-

Security
/ 1 month agoBrazilian LofyGang Returns After Three Years With Minecraft Malware Campaign
A cybercrime group originating from Brazil has resurfaced after more than three years of inactivity to launch a campaign targeting players...
-


Security
/ 1 month agoCritical GitHub RCE Flaw CVE-2026-3854 Exploitable via Git Push
cybersecurity researchers have disclosed a critical security vulnerability affecting GitHub.com and GitHub Enterprise Server. The flaw, designated as CVE-2026-3854, enables an...
-


Security
/ 1 month agoMicrosoft Warns of Active Exploitation in Windows Shell Flaw
Microsoft has revised an advisory for a patched security vulnerability affecting the Windows Shell component, now confirming it is being actively...
-

Security
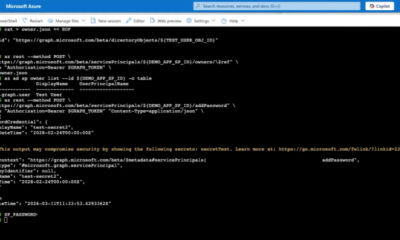
/ 1 month agoEntra ID Flaw Allowed Privilege Escalation via AI Agent Role
A security flaw in a built-in administrative role within Microsoft Entra ID could have Allowed attackers to escalate privileges and take...
-


Security
/ 1 month agoSilk Typhoon Hacker Extradited to US Over COVID Research Attacks
A Chinese national accused of being a member of the state-sponsored hacking group Silk Typhoon has been extradited to the United...