-

Security
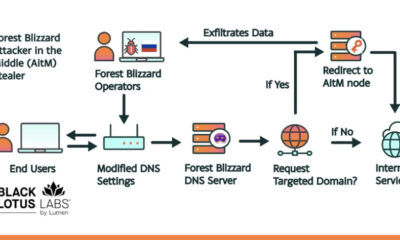
/ 2 months agoRussian APT28 Hijacks Home Routers in Global Cyber Espionage
A Russian state-linked hacking group has compromised thousands of small office and home office routers worldwide, repurposing them for a large-scale...
-


Security
/ 2 months agoIran-Linked Hackers Target U.S. Infrastructure via PLCs
U.S. cybersecurity and intelligence agencies issued a warning on Tuesday that cyber actors affiliated with Iran are actively targeting internet-exposed operational...
-


Security
/ 2 months agoCritical Flowise AI Vulnerability Actively Exploited, Thousands Exposed
Security researchers have confirmed that threat actors are actively exploiting a maximum-severity vulnerability in the open-source Flowise AI platform. The flaw,...
-


Security
/ 2 months agoChina-Linked Hackers Use Zero-Days to Spread Medusa Ransomware
A China-based cyber threat actor has been linked to a series of high-speed attacks that exploit previously unknown software flaws to...
-

Security
/ 2 months agoNew GPU Attack Enables Full System Takeover via Memory Flaws
Academic researchers have identified a new class of hardware-based attacks against modern graphics processing units, or GPUs, that could allow an...
-


Security
/ 2 months agoRecurring Credential Incidents Pose Persistent Financial Threat
New analysis of data breach costs reveals that while major single incidents command attention, the cumulative financial impact of repeated credential...
-


Security
/ 2 months agoIdentity Gaps Persist as AI Threats Loom, Research Finds
A new study has identified a critical security vulnerability within large organizations, where numerous applications operate outside of centralized identity management...
-


Security
/ 2 months agoCryptomining Botnet Targets Over 1,000 Exposed ComfyUI Servers
Security researchers have identified an active campaign that has compromised more than 1,000 internet-exposed servers running ComfyUI, a popular graphical interface...
-

Security
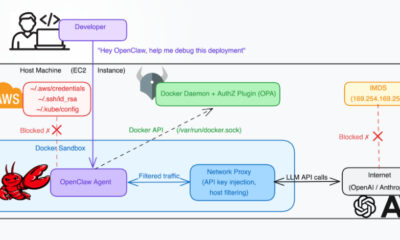
/ 2 months agoDocker Vulnerability CVE-2026-34040 Bypasses Authorization Plugins
A significant security flaw in Docker Engine has been publicly disclosed, allowing attackers to circumvent critical authorization controls under specific conditions....
-


Security
/ 2 months agoNorth Korean Hackers Use GitHub for Attacks on South Korea
cybersecurity researchers have identified a new campaign where threat actors, likely linked to North Korea, are using the public GitHub platform...