-


Security
/ 3 weeks ago18-Year-Old NGINX Flaw Poses Remote Code Execution Risk
Cybersecurity researchers have disclosed multiple security vulnerabilities affecting NGINX Plus and NGINX Open Source, including a critical flaw in the rewrite...
-

Security
/ 3 weeks agoNew Fragnesia Linux LPE Flaw Grants Root Access via Page Cache
A new local privilege escalation vulnerability in the Linux kernel has been disclosed, allowing attackers with local access to gain root...
-

Security
/ 3 weeks agoResearcher Reveals New Windows Zero Day Flaws
An anonymous cybersecurity researcher has disclosed two new zero day vulnerabilities in Microsoft Windows, targeting the BitLocker encryption system and a...
-


Security
/ 3 weeks agoAI Hallucinations Create Real Security Risks in Infrastructure
A growing body of evidence indicates that artificial intelligence systems are introducing serious security risks into critical infrastructure decision-making. These risks...
-


Security
/ 3 weeks agoPraisonAI Flaw Exploited Just Hours After Public Disclosure
Attackers Move Quickly on Critical Vulnerability Threat actors have been observed actively exploiting a recently disclosed security vulnerability in PraisonAI, an...
-

Security
/ 3 weeks agoGhostwriter Group Hits Ukraine With Geofenced Phishing Attacks
A threat actor aligned with Belarus has been linked to a new wave of cyber attacks targeting government agencies in Ukraine....
-

Security
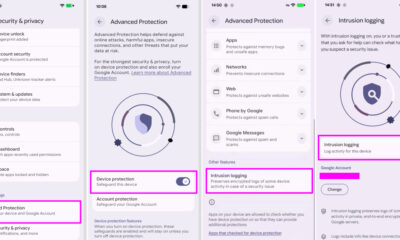
/ 3 weeks agoAndroid adds logging tool to combat advanced spyware threats
Google has introduced a new security feature for Android devices designed to help forensic investigators analyze sophisticated spyware attacks. The feature,...
-


Security
/ 3 weeks agoRubyGems Attack Uses 150+ Packages for Data Theft
cybersecurity researchers have uncovered a campaign targeting the RubyGems repository, involving more than 150 malicious packages. The operation, named GemStuffer by...
-


Security
/ 3 weeks agoMicrosoft Patches 138 Flaws, None Under Active Attack
Microsoft released its monthly security update on Tuesday, addressing 138 vulnerabilities across its software ecosystem. The bundle includes patches for critical...
-


Security
/ 3 weeks agoMost Fixes Remain Unverified as Exploit Times Shrink
According to recent industry data, security teams now have more visibility into their systems than ever before, yet they are failing...