A new software supply chain attack campaign has been observed targeting development infrastructure. Threat actors deployed so called sleeper packages to later push malicious payloads designed for credential theft, GitHub Actions tampering, and SSH persistence.
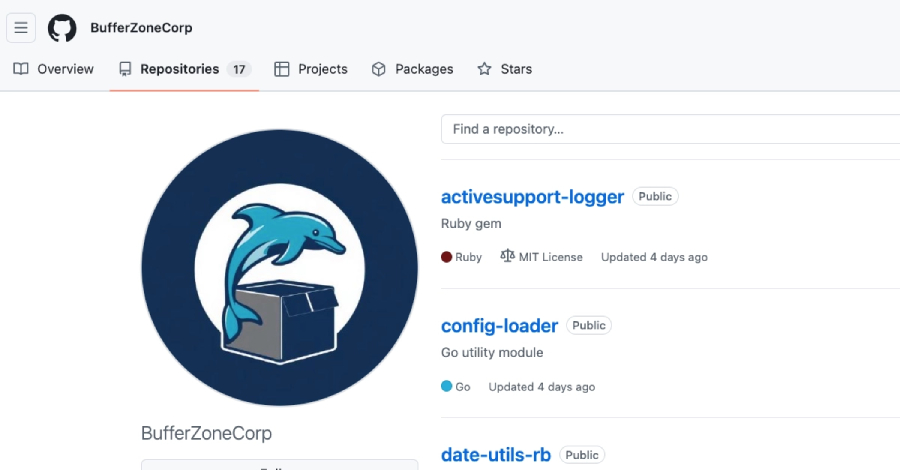
Researchers have attributed the activity to the GitHub account BufferZoneCorp. This account published a set of repositories associated with malicious Ruby gems and Go modules. The campaign highlights a growing trend where attackers poison open source dependencies to compromise downstream users.
How the Attack Works
The campaign relies on sleeper packages. These are seemingly legitimate libraries uploaded to public registries that remain dormant for a period of time. After gaining trust or passing initial security scans, the packages are updated with malicious code.
Once activated, the malicious payloads enable credential theft. This allows attackers to steal API keys, access tokens, and other sensitive data stored in CI/CD pipelines. The attackers also tampered with GitHub Actions workflows to inject further malicious steps. Additionally, they established SSH persistence to maintain long term access to compromised systems.
Targeted Platforms and Scope
The BufferZoneCorp account specifically published repositories containing malicious Ruby gems and Go modules. These libraries are commonly used in software development for web applications and system tools. By poisoning these specific ecosystems, attackers could target a wide range of applications that rely on these dependencies.
The attack demonstrates a sophisticated understanding of supply chain security weaknesses. Instead of directly attacking a single organization, the attackers aimed to compromise the software building blocks that many organizations use. This multiplies the potential impact of the campaign.
Implications for Developers
This incident underscores the risks inherent in using open source dependencies. Developers and security teams must verify the integrity of packages before integrating them into projects. Automated security scanning alone may not catch sleeper packages that activate later.
Organizations should review their CI/CD pipeline configurations. Monitoring for unauthorized changes to workflows and auditing SSH keys for persistence mechanisms are critical steps. The attack also highlights the importance of rotating credentials regularly and limiting the permissions granted to pipeline tokens.
Repositories associated with the threat actor have been identified. Security vendors are likely to update their detection rules to flag code from suspicious accounts. The software supply chain security landscape continues to require vigilance as attackers find new ways to exploit trust in open source ecosystems.
Moving forward, the security community expects increased scrutiny of package updates from new or unfamiliar accounts. Registry maintainers may implement stricter verification processes for publishers. Developers can expect more automated alerts when packages change behavior after initial publication. The full extent of compromised systems remains under investigation.
Source: The Hacker News