-


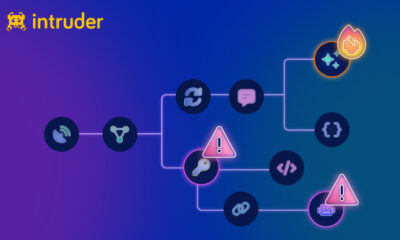
Security
/ 4 weeks agoCritical VM2 Library Vulnerabilities Allow Sandbox Escape
A series of Critical security vulnerabilities have been discovered in the vm2 Node.js library, a widely used open source tool designed...
-

Security
/ 4 weeks agoPyPI Packages Deliver ZiChatBot Malware via Zulip APIs
cybersecurity researchers have identified three malicious packages uploaded to the Python Package Index (PyPI) repository. These packages are designed to covertly...
-

Security
/ 4 weeks agoAI Agents Inside Enterprise Networks Outpace Governance Controls
A new market analysis has confirmed a growing concern for identity security teams: the deployment of artificial intelligence agents within corporate...
-


Security
/ 4 weeks agoHacker News opens submissions for 2026 Cybersecurity Stars Awards
The Hacker News, a long standing publication covering cybersecurity, announced the launch of its “Cybersecurity Stars Awards 2026.” Submissions are now...
-


Security
/ 4 weeks agoMuddyWater Uses Microsoft Teams in False Flag Ransomware Attack
A state-sponsored hacking group linked to the Iranian government has been linked to a disruptive ransomware attack that security researchers describe...
-

Security
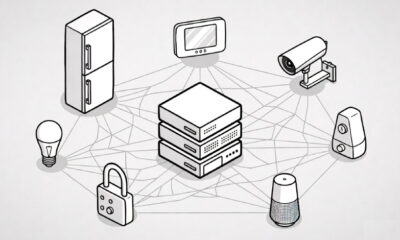
/ 4 weeks agoMirai Botnet Variant Exploits ADB to Hijack IoT Devices
Cybersecurity researchers have identified a new botnet derived from the Mirai malware, self-identified as xlabs_v1, which is actively targeting internet-connected devices...
-


Security
/ 4 weeks agoCritical PAN-OS Flaw Under Active Exploitation Enables Remote Attacks
A critical security vulnerability in Palo Alto Networks’ PAN-OS software is being actively exploited by threat actors, the company confirmed in...
-

Security
/ 4 weeks agoCloudZ RAT Malware Uses New Plugin to Steal Credentials and OTPs
cybersecurity researchers have disclosed details of a recent intrusion campaign that leverages a remote access tool known as CloudZ RAT alongside...
-

Security
/ 4 weeks agoGoogle expands Android app verification to block supply chain attacks
Google has announced an expansion of its Binary Transparency initiative for Android applications, aiming to protect the ecosystem from supply chain...
-

Security
/ 4 weeks agoStudy Exposes Security Flaws in Over 1 Million AI Services
An extensive security audit has revealed critical vulnerabilities across more than one million publicly accessible artificial intelligence services, raising concerns about...