-


Security
/ 2 weeks agoWordPress Funnel Builder Flaw Actively Exploited in WooCommerce Skimming Attacks
A critical security vulnerability in the Funnel Builder plugin for WordPress is now under active exploitation in the wild. Attackers are...
-

Security
/ 2 weeks agoTurla Upgrades Kazuar Backdoor Into Modular P2P Botnet
The Russian state-sponsored hacking group known as Turla has transformed its custom backdoor, Kazuar, into a modular peer-to-peer (P2P) botnet designed...
-


Security
/ 2 weeks agoCISA Adds Cisco SD-WAN Bug to KEV After Exploitation
The United States Cybersecurity and Infrastructure Security Agency (CISA) has added a critical vulnerability affecting Cisco Catalyst SD-WAN Controller to its...
-


Security
/ 2 weeks agoMicrosoft Exchange Server Vulnerability CVE-2026-42897 Exploited
Microsoft has confirmed that a newly disclosed security vulnerability affecting on-premise versions of its Exchange Server is being actively exploited in...
-


Security
/ 2 weeks agoSupply chain attack on TanStack impacts OpenAI employee devices
OpenAI has confirmed that a supply chain attack on the JavaScript library TanStack, known as the “Mini Shai-Hulud” incident, compromised two...
-


Security
/ 2 weeks agoTrusted Admin Tools Reveal True Cyber Attack Surface
Organizations face a significant blind spot in their cybersecurity posture, as the very tools used by IT administrators daily have become...
-


Security
/ 2 weeks agoFour OpenClaw Flaws Enable Data Theft and Privilege Escalation
Cybersecurity researchers have disclosed a set of four security vulnerabilities in the OpenClaw software platform that could be exploited in sequence...
-


Security
/ 3 weeks agoCybersecurity Bulletin Highlights PAN-OS RCE, cURL Bug, and More
A new cybersecurity threat digest has detailed a series of active vulnerabilities and attacks, including a critical remote code execution flaw...
-
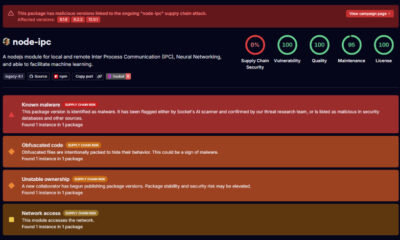

Security
/ 3 weeks agoMalicious Code Found in Three Node-IPC Package Versions
Cybersecurity researchers have issued warnings about malicious activity discovered in newly published versions of the widely used Node IPC package. The...
-


Security
/ 3 weeks agoCisco SD-WAN Controller Zero-Day Flaw Actively Exploited in Attacks
Cisco has confirmed that a critical security vulnerability affecting its Catalyst SD-WAN Controller and Manager products is being Actively exploited in...