-


Security
/ 5 days agoCybersecurity Bulletin: PQC Advances, AI Threats, and Phishing Kits
A recent cybersecurity bulletin highlights a shift towards sophisticated, low-profile threats, including progress in post-quantum cryptography, the weaponization of artificial intelligence...
-


Security
/ 5 days agoCybersecurity Experts Study Art Forgery Tactics for Defense
Security researchers are examining historical art forgery techniques to develop new methods for detecting sophisticated cyberattacks. This cross-disciplinary approach draws direct...
-

Security
/ 5 days agoClaude Extension Flaw Allowed Zero-Click Prompt Injection
A security vulnerability in Anthropic’s Claude browser extension for Google Chrome could have been exploited to silently inject malicious prompts into...
-


Security
/ 5 days agoSecurity Experts Warn of Overconfidence in Cyber Defenses
Security professionals are raising concerns that many organizations may be overestimating the effectiveness of their cybersecurity measures. While security tools are...
-

Security
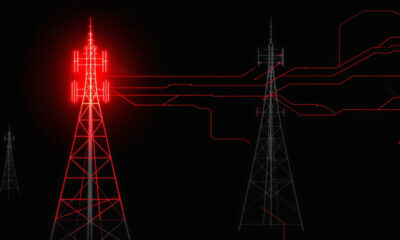
/ 5 days agoChina-Linked Hackers Use BPFDoor Implants in Telecom Espionage
A sophisticated cyber espionage campaign, linked to a China-nexus threat actor, has been discovered targeting telecommunications networks to spy on government...
-

Security
/ 5 days agoNew WebRTC Skimmer Bypasses Security to Steal Payment Data
cybersecurity researchers have identified a novel and sophisticated payment card skimmer that leverages WebRTC data channels to evade standard security defenses...
-

Security
/ 6 days agoMicrosoft 365 Device Code Phishing Campaign Targets Global Orgs
Security researchers have identified an ongoing phishing campaign exploiting Microsoft’s device code authentication to compromise accounts across more than 340 organizations....
-

Security
/ 6 days agoRussian Hacker Jailed for Botnet-Driven Ransomware Scheme
A Russian national has been sentenced to two years in a U.S. federal prison for his role in managing a botnet...
-


Security
/ 6 days agoAI Agent Used in Autonomous Cyber Espionage Campaign
In September 2025, a state-sponsored threat actor used an artificial intelligence coding agent to execute an autonomous cyber espionage campaign. The...
-

Security
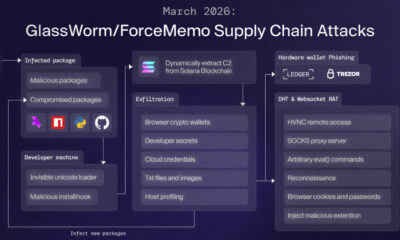
/ 6 days agoGlassWorm Malware Uses Solana for Data Theft and RAT Delivery
cybersecurity researchers have identified a significant evolution in the GlassWorm malware campaign, which now employs the Solana blockchain to deliver a...