Cybersecurity researchers have issued warnings about malicious activity discovered in newly published versions of the widely used Node IPC package. The rogue code, described as a stealer backdoor, targets sensitive developer secrets and credentials stored on affected systems.
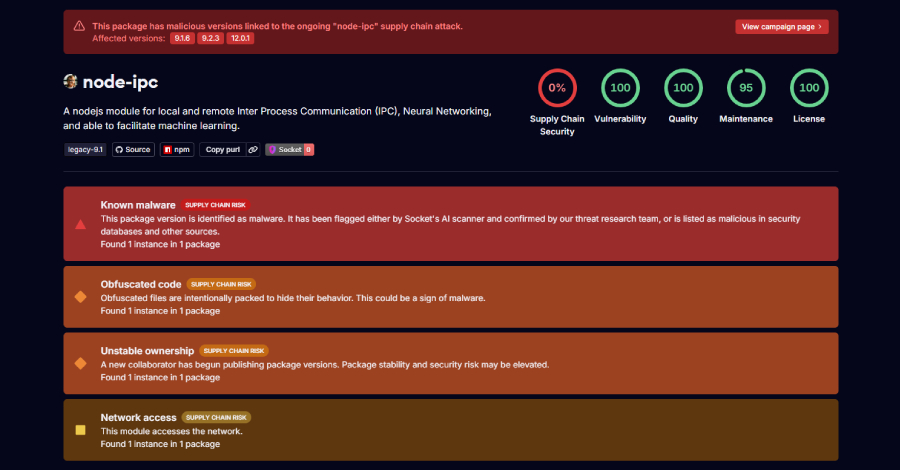
Two security firms, Socket and StepSecurity, have confirmed that three specific versions of the npm package are compromised: node ipc versions 9.1.6, 9.2.3, and 12.0.1. The malicious packages were published to the public npm registry, prompting immediate concern across the developer community.
Early analysis from security researchers indicates that the compromised versions contain hidden functionality designed to exfiltrate private data. The backdoor specifically seeks out developer secrets, including API keys, authentication tokens, and other sensitive configuration files that could grant unauthorized access to internal systems and cloud services.
Node IPC is an inter process communication module for Node.js applications. It is a legitimate and popular package with millions of weekly downloads, making it an attractive vector for supply chain attacks. The package allows different processes on the same machine to communicate, a common requirement for many software development projects.
Technical Details of the Attack
According to the security researchers, the malicious behavior is triggered during the installation of the affected versions. When a developer runs npm install for one of the compromised versions, a post install script executes and attempts to collect data from the host system.
The stolen data is then transmitted to an external server controlled by the attackers. The payload is specifically crafted to locate and extract files commonly used for storing credentials, such as environment variable files, SSH keys, and authentication configuration files.
Socket reported that the malicious code was obfuscated to avoid detection by standard security scanning tools. The obfuscation techniques included encoding the payload and using dynamic code execution methods that are difficult for automated analyzers to flag as suspicious.
Reactions and Remediation
The npm registry has been notified of the security incident. Users who have installed any of the three affected versions are strongly advised to immediately rotate all credentials that may have been exposed on the affected systems.
Developers should also revoke any API keys, tokens, or passwords that were present on the compromised machine. Security teams are recommending a full audit of any systems where the malicious packages were installed to ensure no persistent backdoor remains.
StepSecurity has emphasized the importance of verifying package integrity before installation. The incident underscores the growing threat of software supply chain attacks, where attackers compromise legitimate packages to infect downstream users.
The developers of Node IPC have not yet issued a public statement regarding the breach. The malicious versions have been removed from the npm public repository, but copies may still exist in local caches or private registries.
The attack highlights the inherent risks in open source dependencies. Organizations are encouraged to implement software composition analysis tools and maintain strict update policies to mitigate such threats in the future.
Security experts are also calling for improved vetting processes for npm package submissions, particularly for packages that request network access during installation. The incident is expected to accelerate adoption of cryptographic package signing and automated malicious code scanning within the npm ecosystem.
Developers and organizations using Node.js should review their current dependency lists to confirm they are not using the affected versions. The recommended course of action is to pin dependencies to specific safe versions and to monitor the official Node IPC repository for an updated, clean release.
Source: Delimiter Online