All posts tagged "cybersecurity"
-

Security
/ 1 week agoRussian Hacker Jailed for Botnet-Driven Ransomware Scheme
A Russian national has been sentenced to two years in a U.S. federal prison for his role in managing a botnet...
-


Security
/ 1 week agoAI Agent Used in Autonomous Cyber Espionage Campaign
In September 2025, a state-sponsored threat actor used an artificial intelligence coding agent to execute an autonomous cyber espionage campaign. The...
-

Security
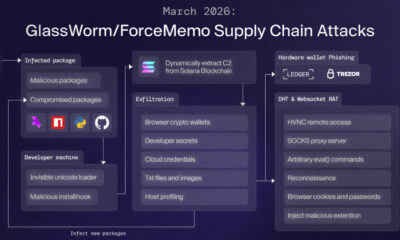
/ 1 week agoGlassWorm Malware Uses Solana for Data Theft and RAT Delivery
cybersecurity researchers have identified a significant evolution in the GlassWorm malware campaign, which now employs the Solana blockchain to deliver a...
-


Security
/ 1 week agoRussian Authorities Arrest Alleged LeakBase Forum Administrator
Russian law enforcement authorities have arrested the alleged administrator of a major cybercrime forum known as LeakBase, according to state media...
-


Security
/ 1 week agoFCC Bans New Foreign Router Imports Over Security Risks
The U.S. Federal Communications Commission (FCC) announced on Monday a ban on the import of new, Foreign-made consumer routers, citing significant...
-


Artificial Intelligence
/ 2 weeks agoDatabricks Acquires Two Startups to Bolster AI Security
Data and artificial intelligence company Databricks has acquired two cybersecurity startups, Antimatter and SiftD.ai. The strategic purchases are intended to strengthen...
-


Security
/ 2 weeks agoCitrix Patches Critical NetScaler Flaw Exposing Sensitive Data
Citrix has issued urgent security updates to address two vulnerabilities in its NetScaler ADC and NetScaler Gateway products. The patches target...
-


Security
/ 2 weeks agoRussian Hacker Sentenced for Role in $9M Ransomware Attacks
A Russian national has been sentenced to six years and nine months in a United States federal prison for his role...
-


Security
/ 2 weeks agoCheckmarx GitHub Actions Compromised by TeamPCP Hackers
A threat actor known as TeamPCP has compromised two GitHub Actions workflows maintained by the software supply chain security firm Checkmarx....
-


Security
/ 2 weeks agoMalicious npm Packages Steal Crypto Wallets in ‘Ghost’ Campaign
cybersecurity researchers have identified a new set of malicious software packages within the widely used npm registry, designed to steal cryptocurrency...

















