All posts tagged "cybersecurity"
-


Tech News
/ 4 days agoFCC Extends Critical Update Waiver for Banned Drones and Routers
The United States Federal Communications Commission has extended a deadline that would have prohibited firmware updates for certain foreign-made drones and...
-


Security
/ 5 days agoOllama Flaw Risks Full Memory Exposure in 300,000 Servers
cybersecurity researchers have disclosed a critical vulnerability in the Ollama artificial intelligence framework that could allow a remote attacker with no...
-


Security
/ 6 days agoGoogle Play Store Fraud: Fake Call Apps Cost Victims Thousands
cybersecurity researchers have uncovered a network of fraudulent applications operating on the official Google Play Store for Android devices. These apps...
-

Security
/ 6 days agoTCLBANKER Trojan Targets Banking and Crypto Platforms
Security researchers have identified a previously undocumented banking trojan targeting financial institutions. The malware, named TCLBANKER, is capable of attacking 59...
-


Security
/ 1 week agoSecurity Bulletin Highlights Edge Vulnerabilities and Urgent Patch Alerts
A new weekly security bulletin has detailed a significant volume of cybersecurity incidents, including exposed plaintext passwords in Microsoft Edge, multiple...
-

Security
/ 1 week agoOne Click Total Shutdown: Webinar Targets Stealth Breaches
cybersecurity professionals are being forced to reconsider their incident response strategies as attackers increasingly rely on artificial intelligence to initiate stealth...
-


Security
/ 1 week agoNew Cloud Credential Theft Framework PCPJack Exploits Five CVEs
cybersecurity researchers have uncovered a new credential theft framework named PCPJack that actively targets exposed cloud infrastructure. The attackers behind this...
-


Artificial Intelligence
/ 1 week agoAnthropic AI helps Mozilla uncover serious Firefox security flaws
Security researchers at Mozilla have identified a significant number of high-severity vulnerabilities in the Firefox web browser, thanks to a new...
-

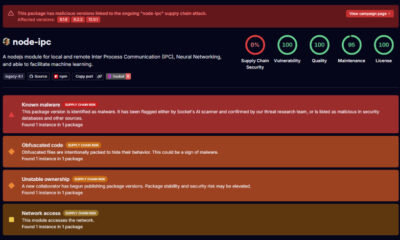
Security
/ 1 week agoPyPI Packages Deliver ZiChatBot Malware via Zulip APIs
cybersecurity researchers have identified three malicious packages uploaded to the Python Package Index (PyPI) repository. These packages are designed to covertly...
-


Security
/ 1 week agoCritical PAN-OS Flaw Under Active Exploitation Enables Remote Attacks
A critical security vulnerability in Palo Alto Networks’ PAN-OS software is being actively exploited by threat actors, the company confirmed in...