All posts tagged "cybersecurity"
-


Security
/ 1 month agoRansomware Negotiator Pleads Guilty in BlackCat Attacks
A Florida man has pleaded guilty to federal charges for his role in assisting the notorious BlackCat ransomware gang in extorting...
-


Security
/ 1 month ago22 Flaws Expose Thousands of Serial-to-IP Converters
cybersecurity researchers have identified 22 new security vulnerabilities in widely used serial-to-IP converter devices from manufacturers Lantronix and Silex. The flaws,...
-


Security
/ 1 month agoSystemBC C2 Server Exposes 1,570+ Ransomware Victims
Security researchers have uncovered a command and control server linked to a known proxy malware, revealing a botnet of more than...
-


Security
/ 1 month agoCISA Adds 8 Exploited Flaws to Catalog, Sets Federal Deadlines
The U.S. cybersecurity and Infrastructure Security Agency (CISA) updated its public catalog of security vulnerabilities on Monday, adding eight new entries...
-

Security
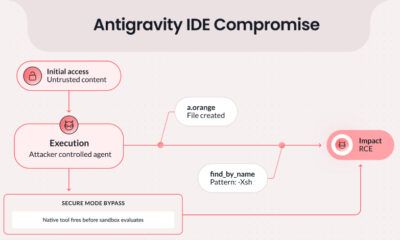
/ 1 month agoGoogle Patches Antigravity IDE Vulnerability Enabling Code Execution
Google has addressed a security vulnerability in its Antigravity integrated development environment, or IDE, that could have allowed attackers to execute...
-


Security
/ 1 month agoAndroid Malware Trojanizes HandyPay App to Steal NFC Data
cybersecurity researchers have identified a new campaign targeting Android users in Brazil, where a known malware family has been modified to...
-


Security
/ 1 month agoIdentity Attacks Overtake Exploits as Top Breach Method
Security researchers report a significant shift in cyberattack strategies, with identity-based attacks now surpassing software exploits as the most common initial...
-


Internet of Things
/ 1 month agoValmet Partners with Elisa to Secure Industrial IoT Systems
Finnish industrial technology company Valmet has entered a strategic partnership with telecommunications operator Elisa to establish a global Cybersecurity operations center....
-


Security
/ 1 month agoWeekly Cybersecurity Recap: Supply Chain Attacks and New Threats
A series of <a href="https://delimiter.online/blog/zionsiphon-malware/” title=”cybersecurity”>cybersecurity incidents reported this week highlight a continued focus by threat actors on exploiting trusted software...
-


Security
/ 1 month agoCritical SGLang Vulnerability Enables Remote Code Execution
A critical security vulnerability in the SGLang framework, tracked as CVE-2026-5760, could allow attackers to execute arbitrary code on vulnerable systems....