-


Security
/ 1 month agoModern SOC Teams Use AI for Faster Cloud Breach Investigations
Security operations center teams are increasingly adopting artificial intelligence and contextual data analysis to accelerate investigations into cloud based breaches, according...
-

Security
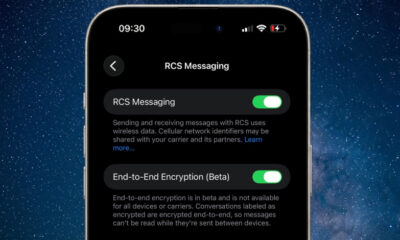
/ 1 month agoApple Tests Encrypted RCS Messaging in iOS Beta
Apple has introduced a significant upgrade to its messaging infrastructure by enabling end-to-end encryption for RCS communications in its latest developer...
-


Security
/ 1 month agoNew ZeroDayRAT Mobile Spyware Threatens Android and iOS Users
cybersecurity researchers have uncovered a new and sophisticated mobile spyware platform being actively marketed to potential buyers. The malware, known as...
-


Security
/ 1 month agoLithuania Launches Mission to Combat AI Cyber Fraud
A consortium led by Kaunas University of Technology (KTU) presented its mission to build a safe and inclusive digital society at...
-


Security
/ 1 month agoWeekly Security Recap: Add-In Hijacks, Zero-Days, Botnets
Security researchers have documented a significant shift in cyberattack strategies over the past week, where trusted software tools and established workflows...
-


Security
/ 1 month agoMajor Password Managers Vulnerable to Recovery Attacks
A recent academic study has identified significant vulnerabilities in several leading cloud-based password management services. The research found that under specific...
-


Security
/ 1 month agoInfostealer Targets AI Agent Configurations and Tokens
cybersecurity researchers have disclosed a new type of information stealer attack that successfully exfiltrated configuration files and gateway tokens for an...
-

Security
/ 1 month agoGoogle Patches Actively Exploited Chrome Zero-Day Vulnerability
Google has released an urgent security update for its Chrome web browser to address a critical vulnerability that is already being...
-

Security
/ 1 month agoMicrosoft Discloses DNS-Based ClickFix Attack Using Nslookup
Microsoft has disclosed details of a new version of a social engineering attack, dubbed ClickFix, that tricks users into running commands...
-

Security
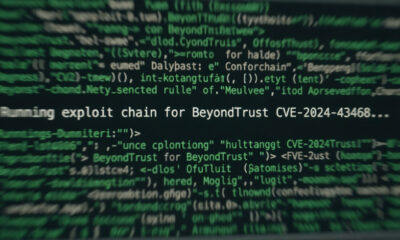
/ 2 months agoBeyondTrust Vulnerability Actively Exploited by Attackers
Threat actors have begun actively exploiting a critical security vulnerability in BeyondTrust’s Remote Support and Privileged Remote Access software. The cybersecurity...


















