-


Security
/ 2 months agoSilver Fox Hackers Target Asia with New RAT and Fake Domains
A sophisticated cyber espionage campaign is actively targeting Chinese-speaking users across Asia, deploying a previously undocumented remote access trojan through counterfeit...
-

Security
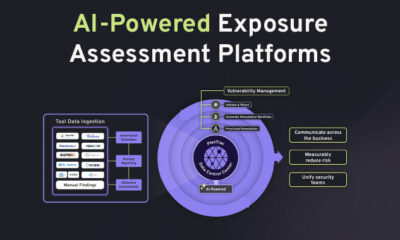
/ 2 months agoAI Arms Race Elevates Cybersecurity to Board Level Priority
The global cybersecurity landscape is undergoing a fundamental shift, driven by the rapid weaponization of artificial intelligence by threat actors. This...
-


Security
/ 2 months agoGoogle Cloud Vertex AI Flaw Exposes Sensitive Data
cybersecurity researchers have disclosed a security vulnerability within Google Cloud‘s Vertex AI platform that could enable attackers to misuse artificial intelligence...
-


Security
/ 2 months agoTrueConf Zero-Day Exploited in Southeast Asian Government Attacks
A critical security vulnerability in the TrueConf video conferencing software has been actively exploited as a zero-day in targeted attacks against...
-


Security
/ 2 months agoGoogle Begins Android Developer Verification Rollout
Google has officially begun a global rollout of its Android developer verification program, the company announced on Monday. The initiative is...
-


Security
/ 2 months agoAxios npm Package Compromised in Supply Chain Attack
Two versions of the widely used Axios HTTP client library were found to contain malicious code this week, following a compromise...
-


Security
/ 2 months agoSOC Process Improvements Boost Tier 1 Analyst Productivity
security operations centers globally are identifying process inefficiencies, not just sophisticated threats, as a primary barrier to analyst productivity. According to...
-

Security
/ 2 months agoTelecom Espionage, AI Vulnerabilities, and UK Age Verification Updates
Legal proceedings have begun against alleged long-term espionage operations within telecommunications infrastructure, while new research demonstrates vulnerabilities in large language models....
-

Security
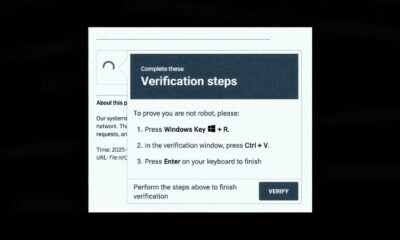
/ 2 months agoDeepLoad Malware Uses Social Engineering to Steal Browser Data
A newly identified malware loader, dubbed DeepLoad, is being distributed through a sophisticated social engineering campaign targeting users worldwide. The campaign...
-

Security
/ 2 months agoOpenAI Fixes Critical ChatGPT Data Leak and GitHub Token Flaw
A significant security vulnerability in OpenAI‘s ChatGPT allowed unauthorized extraction of user conversation data, according to research from cybersecurity firm Check...