-


Security
/ 1 month agoCybersecurity Predictions for 2026 Forecast Permanent Instability
cybersecurity experts are predicting a fundamental shift in the digital threat landscape for 2026, moving from periodic crises to a state...
-

Security
/ 1 month agoCritical Flaws Found in Four Popular VS Code Extensions
cybersecurity researchers have disclosed multiple security vulnerabilities in four widely used Microsoft Visual Studio Code extensions. The flaws, if exploited, could...
-

Security
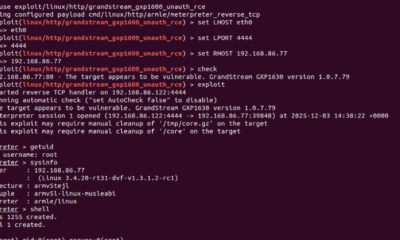
/ 1 month agoCritical Flaw in Grandstream VoIP Phones Allows Remote Takeover
Cybersecurity researchers have disclosed a critical security vulnerability in the Grandstream GXP1600 series of VoIP phones that could allow attackers to...
-


Security
/ 1 month agoCellebrite Tool Used on Kenyan Activist’s Phone in Custody
New research has uncovered evidence that Kenyan authorities used a commercial phone hacking tool to access the device of a prominent...
-


Security
/ 1 month agoCISA Adds Four Actively Exploited Flaws to KEV Catalog
The U.S. cybersecurity and Infrastructure Security Agency (CISA) updated its Known Exploited Vulnerabilities (KEV) catalog on Tuesday, adding four security flaws....
-

Security
/ 1 month agoMicrosoft Uncovers AI Chatbot Manipulation via Summarize Feature
Microsoft security researchers have identified a new technique used by businesses to manipulate the recommendations of artificial intelligence chatbots. The method...
-


Security
/ 1 month agoHands-On NDR Training Provides Insight into Network Security Operations
A recent Hands-On training session with a Network Detection and Response (NDR) platform offered a practical look into the tools and...
-

Security
/ 1 month agoTrojanized Oura MCP Server Deploys StealC Infostealer
cybersecurity researchers have identified a new campaign distributing the SmartLoader malware, which uses a trojanized version of a legitimate Model Context...
-

Security
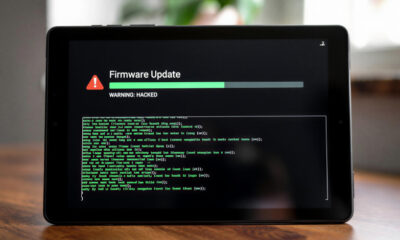
/ 1 month agoAndroid Tablet Firmware Backdoor Found in Signed Updates
Security researchers have discovered a sophisticated backdoor embedded within the firmware of several Android tablet brands. The malware, which is distributed...
-


Security
/ 1 month agoAI Assistants Exploited as Malware Command Hubs
cybersecurity researchers have revealed that popular artificial intelligence assistants can be manipulated to act as covert communication channels for malware. This...


















