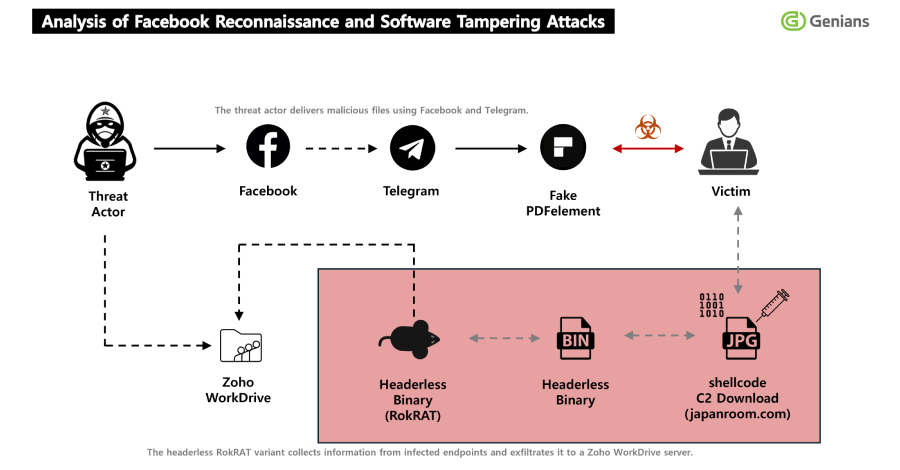
A state-sponsored North Korean hacking group has been linked to a new social engineering campaign that uses Facebook friend requests to infect targets with sophisticated malware. The group, tracked by cybersecurity researchers as APT37, also known as ScarCruft, is believed to be behind the operation, which delivers a remote access trojan called RokRAT.
The campaign involves threat actors creating fake Facebook profiles to approach potential victims. After sending a friend request, the attackers engage in conversation to build trust. Once a rapport is established, they deliver malicious files disguised as documents or photos.
How the Social Engineering Attack Works
According to security analysts, the threat actor used two distinct Facebook accounts in this campaign. The profiles presented themselves as journalists or media professionals from Southeast Asia, a region of strategic interest to North Korea. This guise was designed to appeal to individuals working in government, academia, or think tanks.
The initial contact on the social media platform is followed by casual conversation. The attackers then shift the discussion to topics of purported professional interest. They eventually send a file, often via a link to a cloud storage service, claiming it contains important research, photographs, or a document related to the discussion.
The Role of RokRAT Malware
The file delivered is not a benign document but a loader for RokRAT. This malware is a full-featured remote access trojan (RAT) associated with APT37. Once executed on a victim’s computer, it can steal files, capture screenshots, log keystrokes, and execute additional commands sent from the attackers’ control servers.
RokRAT has been a tool in APT37’s arsenal for several years and is considered a signature of the group’s cyber espionage activities. Its use in this Facebook-based campaign represents an evolution in the group’s tactics, moving from spear-phishing emails to exploiting the trust inherent in social media connections.
Attribution and Historical Context
APT37 is a cyber espionage group believed to operate on behalf of the North Korean government. Security firms have linked the group to attacks targeting South Korean entities, Japanese organizations, and global defense contractors. Their objectives typically involve intelligence gathering and theft of sensitive information.
The group’s alias, ScarCruft, is widely used within the cybersecurity community. Their operations are characterized by a high degree of planning and a focus on specific, high-value targets rather than broad, opportunistic attacks.
Implications for Social Media Security
This campaign highlights the growing trend of nation-state actors leveraging mainstream social media platforms for targeted attacks. The use of Facebook demonstrates how attackers exploit human psychology and the normalized practice of connecting with professional contacts online.
Security experts note that such attacks are difficult for platform algorithms to detect because they rely on genuine, albeit deceptive, human interaction over an extended period. The malicious payload is delivered outside the platform’s direct messaging system, further evading automated security scans.
Recommended Defensive Measures
Organizations and individuals, particularly those in sectors of geopolitical interest, are advised to exercise heightened caution with unsolicited contact on social media. Verifying the identity of new connections through secondary channels is a recommended best practice.
Cybersecurity professionals stress the importance of not downloading or executing files from unverified sources, even if they arrive via a trusted platform like Facebook. Maintaining updated endpoint security software and employing application allow-listing can help mitigate the risk of infection from such targeted attacks.
Based on the established patterns of APT37, cybersecurity researchers anticipate continued monitoring of the group’s infrastructure and the release of further technical indicators of compromise (IOCs) to help network defenders block this threat. Law enforcement and Facebook’s security team are likely investigating the fake accounts used in this campaign, which may lead to their takedown in the coming weeks.
Source: Multiple cybersecurity intelligence reports