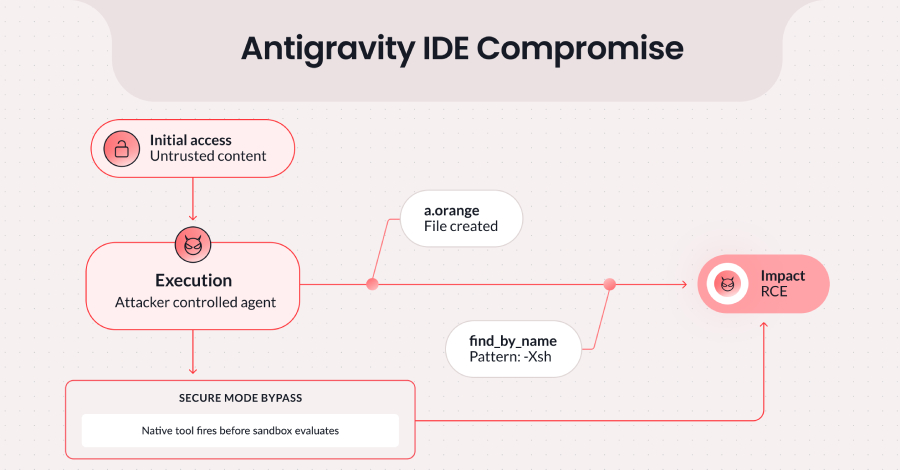
Google has addressed a security vulnerability in its Antigravity integrated development environment, or IDE, that could have allowed attackers to execute malicious code. The flaw, which has now been patched, was discovered by cybersecurity researchers and stemmed from a combination of features within the cloud based development tool.
The issue specifically involved Antigravity’s ability to create files and a separate, native file searching tool called “find_by_name.” According to the technical disclosure, insufficient input sanitization in the search tool could be chained with the file creation permissions to bypass the environment’s security restrictions.
Technical Details of the Flaw
The vulnerability, categorized as a prompt injection attack vector, exploited the trust boundary between different components of the Antigravity IDE. The “find_by_name” tool, designed to help developers locate files within their projects, did not adequately validate or sanitize user input. This oversight allowed for crafted inputs that, when processed, could lead to unintended behavior.
By combining this weakness with Antigravity’s inherent capability to write new files to the workspace, a threat actor could potentially create and then execute arbitrary code within the environment. This would effectively break the “Strict” security model intended to isolate and protect the development workspace from such actions.
Google’s Response and Patch
Upon being notified by security researchers, Google’s development team moved to correct the vulnerability. The company has released updates and backend fixes that enhance input validation within the “find_by_name” utility and reinforce the security boundaries of the Antigravity IDE.
Google has not indicated that the vulnerability was actively exploited in the wild before the patch was applied. The company’s standard security protocols were followed, involving private disclosure and a coordinated fix before public announcement to minimize potential risk to users.
Broader Implications for Developer Tools
This incident highlights the evolving security challenges facing cloud native and AI assisted development platforms. As IDEs like Antigravity incorporate more agentic, or autonomous, features and deeper integrations, the attack surface can expand in unexpected ways. The flaw demonstrates how seemingly benign features, when interacting, can create critical security gaps.
Security experts note that prompt injection attacks, often discussed in the context of large language models, can also manifest in other systems that process complex, user supplied instructions. The Antigravity case serves as a reminder for developers and platform engineers to rigorously audit the interactions between all system components, even those with limited individual privileges.
For developers using the Antigravity IDE, ensuring their workspace is updated to the latest version is the primary recommended action. No additional steps are required, as the fix is deployed server side and through automatic client updates.
Looking forward, the security community expects increased scrutiny on the architecture of AI enhanced development environments. Further research into secure prompt handling and feature isolation within these platforms is likely to continue, with similar vulnerabilities potentially being discovered and disclosed in a responsible manner by other firms in the sector.
Source: Based on technical security disclosure