cybersecurity researchers have uncovered a new digital fraud scheme that uses artificial intelligence and search engine manipulation to place deceptive news articles into Google’s Discover feed. The campaign, active in recent months, aims to trick users into enabling browser notifications that subsequently deliver scareware and financial scams.
Mechanics of the Campaign
The operation, dubbed “Pushpaganda” by security analysts, begins with the creation of fraudulent news websites. These sites use AI to generate large volumes of content designed to rank highly in search results for trending topics. This technique, known as search engine poisoning or SEO poisoning, gives the sites an appearance of legitimacy.
Once established in search rankings, the sites’ content is promoted into the Google Discover feed, a personalized content stream used by millions on mobile devices. The articles often feature sensational or alarming headlines about celebrities, current events, or fake product recalls to attract clicks.
The User Trap
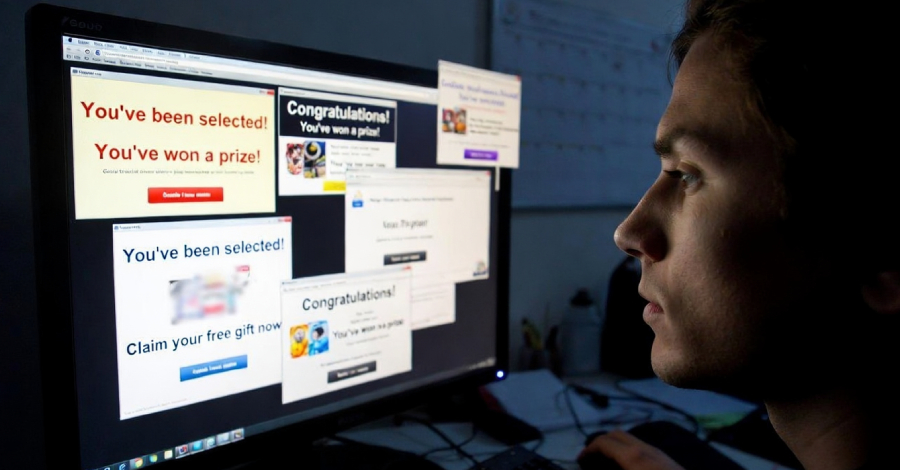
Upon visiting one of these sites, users are immediately presented with a prompt asking to “allow notifications” from their browser. The prompt is often disguised as a required step to read the article, verify human identity, or view a video.
If a user clicks “allow,” they grant permission for the scam operators to send direct notifications to their desktop or mobile device. These notifications then bypass the website and deliver messages directly to the user’s operating system.
From Notifications to Scams
The persistent notifications become the primary attack vector. They are used to deliver fake security alerts, known as scareware, which falsely warn users that their device is infected with viruses. The alerts direct users to download malicious software or call fraudulent tech support numbers.
Other notifications lead to ad fraud schemes, redirecting users to phishing pages, fraudulent lotteries, or deceptive subscription services. The operators generate revenue through pay-per-click advertising fraud and by selling access to the notification delivery channel to other cybercriminals.
Scale and Impact
Researchers report that the campaign has created hundreds of domains and generated thousands of AI-authored articles. The scale allows it to target a global audience, though specific regional focuses have been observed. The financial impact on individual victims can range from fraudulent charges to costly fake software purchases.
Google Discover’s algorithm, which surfaces content based on a user’s search history and interests, inadvertently amplifies the reach of these malicious sites. The campaign exploits the automated nature of content curation in such feeds.
Industry and Platform Response
Security firms have notified Google of the domains involved in the Pushpaganda campaign. Google has stated it uses a combination of automated systems and human review to enforce its policies against deceptive content on Discover and in search results.
The company removes sites that violate its policies, which explicitly prohibit practices like misleading users into subscribing to notifications or distributing harmful software. However, the dynamic nature of the threat requires continuous monitoring.
Protection and Next Steps
Experts advise users to be extremely cautious when encountering notification permission prompts, especially on unfamiliar news sites. They recommend denying such requests unless from a trusted, well-known website. Users who have accidentally allowed notifications can revoke the permission in their browser’s settings menu.
Looking ahead, cybersecurity analysts expect threat actors to continue refining these techniques, potentially using more sophisticated AI to create even more convincing fake news content. The security community anticipates increased collaboration with platform providers like Google to identify and dismantle the infrastructure behind these campaigns more swiftly. Ongoing user education about browser notification risks remains a critical defense.
Source: Various Cybersecurity Research Reports