A security vulnerability in LMDeploy, an open source toolkit designed for compressing, deploying, and serving large language models, has been actively exploited in the wild less than 13 hours after the flaw was publicly disclosed.
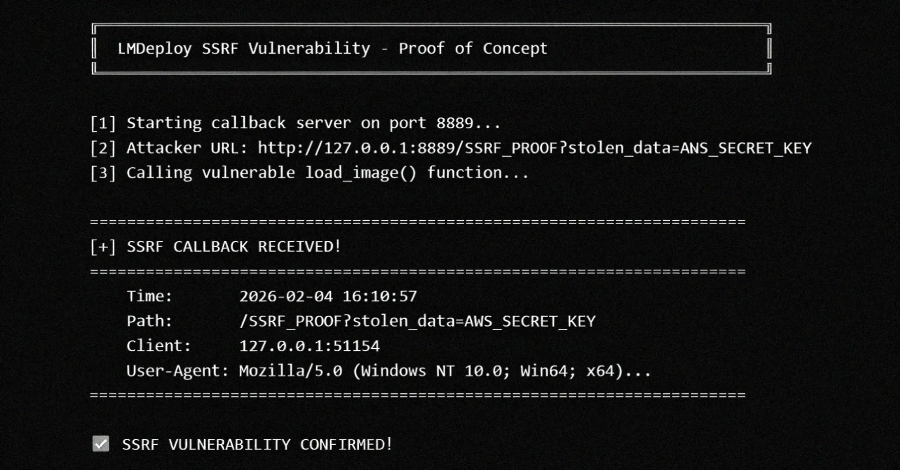
The vulnerability, formally designated CVE-2026-33626, carries a CVSS severity score of 7.5 out of 10, placing it in the high severity category. The issue is a Server Side Request Forgery (SSRF) vulnerability, which can allow an attacker to send crafted requests from the server to internal systems.
What Is LMDeploy and Why This Matters
LMDeploy is widely used in the artificial intelligence development community for managing and deploying large language models in production environments. An SSRF vulnerability in such a tool is particularly concerning because it could enable attackers to bypass firewalls and access sensitive data stored on internal networks.
Server Side Request Forgery is a type of security flaw where an attacker can induce a server to make HTTP requests to an arbitrary domain of the attacker’s choosing. In this case, the flaw could be exploited to access data that would otherwise be protected behind network perimeters.
The rapid exploitation timeline, occurring within 13 hours of public disclosure, indicates that threat actors are actively scanning for newly disclosed vulnerabilities. This pattern is increasingly common in the security landscape as automated scanning tools can rapidly identify and target vulnerable systems.
Potential Impact and Affected Versions
While specific version numbers affected by CVE-2026-33626 have not been fully detailed in public advisories, users of LMDeploy are urged to review their deployments and apply any available patches promptly. The SSRF nature of the vulnerability means that organizations using LMDeploy in internal or cloud hosted environments could be at risk of data exfiltration.
Attackers exploiting this vulnerability could potentially access cloud metadata services, internal APIs, or other sensitive endpoints that are not intended to be exposed to the public internet. The speed of exploitation also suggests that proof of concept code may have been published or shared among threat actors shortly after disclosure.
Security researchers have noted that the 13 hour window between disclosure and active exploitation is alarmingly short, leaving system administrators little time to apply patches or implement mitigations. This underscores the importance of automated patch management and vulnerability scanning in modern IT environments.
Recommendations for Security Teams
Organizations using LMDeploy should immediately check their systems for signs of compromise. Indicators of compromise may include unusual outbound network connections from servers running LMDeploy, especially connections to unfamiliar external hosts or internal IP addresses that should not be reachable.
Network segmentation can help limit the blast radius of any SSRF exploitation. Ensuring that LMDeploy servers do not have unrestricted access to internal resources is a key mitigation strategy. Web application firewalls and network monitoring tools can also help detect and block SSRF based attacks.
The security community continues to monitor the situation, and further technical details are expected in the coming days from both the LMDeploy project maintainers and independent security researchers. Organizations are advised to subscribe to security advisories from the LMDeploy project and related infrastructure vendors.
This incident highlights a broader trend in the software supply chain and artificial intelligence infrastructure sectors, where vulnerabilities in popular developer tools can have widespread consequences. The exploitation of CVE-2026-33626 serves as a reminder that disclosure timelines are shrinking and that proactive security hygiene is more critical than ever.
As of this writing, no widespread reports of data breaches directly linked to this vulnerability have been confirmed, but the active exploitation indicates that attackers are actively attempting to leverage the flaw. System administrators should treat this as an urgent security event and prioritize patching and investigation.
Source: Delimiter Online