Security researchers have uncovered a sophisticated phishing campaign that compromised approximately 30,000 Facebook accounts by using Google AppSheet as a relay for fraudulent emails. The operation, linked to Vietnamese threat actors, has been tracked under the codename AccountDumpling by cybersecurity firm Guardio.
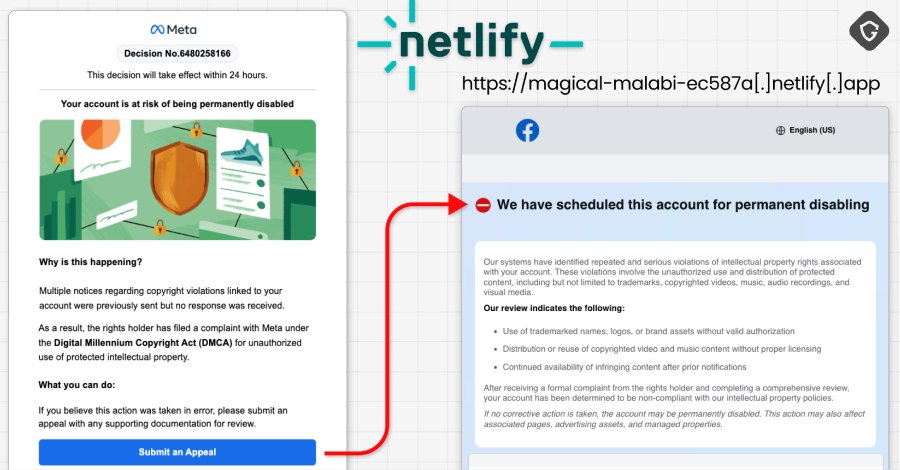
The campaign relied on Google AppSheet, a legitimate low-code application development platform, to bypass traditional email security filters. Attackers crafted phishing emails that appeared to originate from trusted sources by abusing the platform’s notification and authentication features. Victims who clicked on embedded links were redirected to counterfeit Facebook login pages designed to capture their credentials.
How the Scheme Operated
Guardio’s analysis revealed that the phishing emails were structured to look like standard account recovery or security alerts from Facebook. The use of Google AppSheet added an additional layer of legitimacy, as the emails carried a trusted domain and passed many standard email authentication checks.
Once users entered their login information on the fake pages, the stolen credentials were harvested and used to gain unauthorized access to the victims’ Facebook accounts. The attackers then sold these compromised accounts through an illicit storefront, which Guardio identified as part of the AccountDumpling operation.
Scale and Impact
The campaign succeeded in compromising roughly 30,000 Facebook accounts before it was identified and disrupted. Guardio stated that the stolen accounts were marketed and sold via a dedicated underground marketplace run by the same threat actors. The exact financial scope of the operation remains unclear, but researchers noted that the sale of compromised social media accounts can generate significant revenue for cybercriminals.
Facebook accounts are a frequent target for phishing due to their use in personal communications, business marketing, and as gateways to other linked services. Compromised accounts can be exploited for spam distribution, identity theft, and further phishing attacks against the victim’s network.
Technical Details and Mitigation
Guardio’s researchers emphasized that the attack exploited a legitimate platform rather than a software vulnerability. Google AppSheet’s ability to send automated notifications and process webhooks allowed the attackers to relay phishing content without needing to host malicious infrastructure on their own domains. This made the emails harder for automated security tools to detect as malicious.
Security experts recommend that users enable two-factor authentication on their Facebook accounts and remain cautious of any email requesting login credentials or personal information, even if the message appears to come from a trusted source. Organizations using low-code platforms like AppSheet should also review their security configurations to prevent similar abuse.
As of the latest reports, the AccountDumpling storefront has been taken offline, but researchers warn that the threat actors may relaunch similar campaigns using alternative platforms or techniques. Facebook has not issued a public statement specifically addressing this campaign, but the company routinely advises users to report suspicious emails and avoid clicking on links in unsolicited messages.
Source: Guardio