-


Security
/ 2 months agoIranian Hackers Resume Operations with New Infrastructure
A sophisticated Iranian cyber threat group has resumed its activities with updated infrastructure, following a period of reduced visibility that coincided...
-

Security
/ 2 months agoAI Security Gap Widens as Enterprise Use Outpaces Controls
A significant gap has emerged between the rapid adoption of artificial intelligence tools in business environments and the security measures designed...
-


Security
/ 2 months agoCybersecurity Threats Emerge from Developer Tools and Cloud Services
Security researchers have identified a series of emerging cyber threats targeting software development environments, remote administration tools, and cloud infrastructure. These...
-

Security
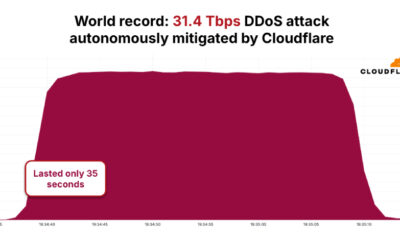
/ 2 months agoBotnet Sets Record with 31.4 Tbps DDoS Attack
A distributed denial-of-service botnet known as AISURU or Kimwolf has been linked to a record-breaking cyberattack that reached a peak of...
-


Security
/ 2 months agoMalicious NGINX Configurations Hijack Web Traffic
cybersecurity researchers have uncovered an ongoing, large-scale campaign that is hijacking web traffic by compromising NGINX web servers and related management...
-


Security
/ 2 months agoCritical n8n Vulnerability Allows Remote Code Execution
A critical security vulnerability in the popular n8n workflow automation platform could allow attackers to execute arbitrary system commands on affected...
-


Security
/ 2 months agoEarly Decisions in First 90 Seconds Critical to Incident Response
The initial moments following the detection of a security breach are now widely regarded as the most critical phase of any...
-

Security
/ 2 months agoOrchid Security Launches Continuous Identity Observability Platform
A cybersecurity firm has introduced a new platform designed to provide continuous monitoring of identity usage within enterprise software applications. The...
-

Security
/ 2 months agoChina-Linked Hackers Exploit WinRAR Flaw in Southeast Asia Espionage
Security researchers have identified a new cyber espionage campaign targeting government and law enforcement agencies across Southeast Asia throughout 2025. The...
-


Security
/ 2 months agoDEAD#VAX Malware Uses IPFS VHD Files to Deploy AsyncRAT
Security researchers have uncovered a sophisticated malware campaign, identified as DEAD#VAX, which uses a novel combination of legitimate system features and...