-


Security
/ 2 months agoCISOs Address Burnout and MTTR Without New Hires
Chief Information Security Officers (CISOs) at leading organizations are implementing new operational strategies to combat analyst burnout and improve security response...
-

Security
/ 2 months agoWeekly Cybersecurity Recap: AI Malware, DDoS Attacks, and Supply Chain Threats
Cyber threats are increasingly emerging from within the trusted tools and platforms that organizations rely on daily. This week, security researchers...
-


Security
/ 2 months agoOpenClaw Integrates VirusTotal to Scan ClawHub Skills for Security
The automation platform OpenClaw has integrated VirusTotal’s threat intelligence to scan all skills uploaded to its ClawHub marketplace. This partnership, announced...
-


Security
/ 2 months agoGerman Agencies Warn of Signal Phishing Targeting Officials
German security agencies have issued a joint warning about a sophisticated phishing campaign conducted over the Signal messaging application, targeting high-profile...
-


Security
/ 2 months agoAsian Cyber Espionage Group Breaches 70 Global Entities
A previously undocumented cyber espionage group, operating from Asia and backed by a state, has successfully infiltrated the networks of at...
-


Security
/ 2 months agoCISA Mandates Removal of Outdated Federal Network Devices
The U.S. cybersecurity and Infrastructure Security Agency (CISA) has directed federal agencies to identify and remove unsupported edge network devices from...
-

Security
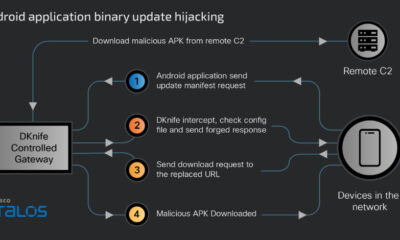
/ 2 months agoChina-Linked DKnife Framework Hijacks Router Traffic for Malware
cybersecurity researchers have exposed a sophisticated adversary-in-the-middle framework, known as DKnife, which has been operated by threat actors linked to China...
-

Security
/ 2 months agoAI Model Discovers 500+ Critical Flaws in Open-Source Libraries
An artificial intelligence system has identified more than 500 previously unknown, high-severity security vulnerabilities across widely used open-source software libraries. The...
-


Security
/ 2 months agoCompromised dYdX npm and PyPI Packages Deliver Malware
Cybersecurity researchers have identified a software supply chain attack targeting developers working with the dYdX decentralized exchange. Malicious actors have compromised...
-


Security
/ 2 months agoSamsung Knox Addresses Mobile Security in Evolving Enterprise Networks
Enterprise network security has undergone significant evolution over the past decade, with more intelligent firewalls, advanced threat detection, and detailed access...


















