-

Security
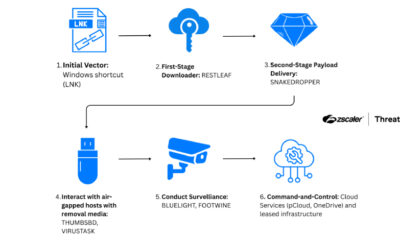
/ 1 month agoNorth Korean Hackers Target Air-Gapped Networks via Cloud and USB
A North Korean state-sponsored hacking group has been observed using a novel combination of cloud-based and physical media malware to infiltrate...
-


Security
/ 1 month agoWeekly Security Bulletin Highlights Emerging Cyber Threats
A new weekly security bulletin has detailed over fifteen significant cybersecurity threats and developments observed globally. The report, compiled from industry...
-


Security
/ 1 month agoNew Backdoor Targets US Education and Healthcare Sectors
A previously undocumented cyber threat campaign has been targeting organizations within the education and healthcare sectors in the United States since...
-

Security
/ 1 month agoBotnet Uses Polygon Blockchain to Evade Security Takedowns
cybersecurity researchers have disclosed a new botnet loader that uses a public blockchain to store its commands, creating a resilient infrastructure...
-


Security
/ 1 month agoCisco SD-WAN Zero-Day Exploited Since 2023 for Admin Access
A critical, unpatched vulnerability in widely used Cisco networking software has been actively exploited by attackers for over a year to...
-


Security
/ 1 month agoMalicious NuGet Package Impersonates Stripe Library to Steal Tokens
cybersecurity researchers have disclosed a new malicious software package found on the NuGet Gallery, a major repository for .NET developers. The...
-

Security
/ 1 month agoMicrosoft Warns of Fake Next.js Job Repos Spreading Malware
Microsoft has issued a warning to software developers about a coordinated campaign using fake job listings and counterfeit code repositories to...
-


Security
/ 1 month agoCybersecurity Experts Urge Immediate Preparation for Post-Quantum Encryption
cybersecurity professionals are issuing a clear directive to organizations and governments worldwide: begin preparing for the transition to post-quantum cryptography immediately....
-


Security
/ 1 month agoMalicious NuGet Packages Target ASP.NET Developers, Steal Data
cybersecurity researchers have identified a new campaign involving four malicious packages on the NuGet repository, a key software library for .NET...
-


Security
/ 1 month agoFlawed Security Triage Increases Business Risk, Analysts Report
security operations centers globally are reporting that ineffective triage processes are increasing business risks rather than mitigating them, according to industry...


















