-

Security
/ 4 weeks agoSecurity Leaders Advised on Quantum Computing Threats
Security leaders globally are being urged to prepare for the threat quantum computers pose to current encryption standards, a risk that...
-


Security
/ 4 weeks agoCisco Confirms Active Attacks Exploiting SD-WAN Manager Flaws
Cisco Systems has confirmed that two security vulnerabilities in its Catalyst SD-WAN Manager software are now being actively exploited by attackers....
-


Security
/ 4 weeks agoCISA Adds VMware Flaw to Exploited Vulnerabilities List
The U.S. cybersecurity and Infrastructure Security Agency (CISA) added a high-severity security vulnerability in VMware Aria Operations to its Known Exploited...
-


Security
/ 4 weeks agoAPT41-Linked Silver Dragon Targets Governments with Cobalt Strike
cybersecurity researchers have disclosed details of an advanced persistent threat group, dubbed Silver Dragon, which has been linked to cyber attacks...
-


Security
/ 4 weeks agoMalicious Laravel Packages on Packagist Spread Cross-Platform RAT
cybersecurity researchers have identified a series of malicious packages within the official Packagist repository for PHP, posing as legitimate Laravel utilities...
-

Security
/ 4 weeks agoNew RFP Template Aims to Standardize AI Governance
Technology and security leaders have released a new standardized template to help organizations formally request and evaluate solutions for controlling artificial...
-


Security
/ 4 weeks agoGoogle Exposes Coruna iOS Exploit Kit Targeting iPhones
Google has identified a new and powerful exploit kit, named Coruna, targeting Apple iPhones running iOS versions 13.0 through 17.2.1. The...
-


Security
/ 4 weeks agoHacktivist DDoS Attacks Surge After Middle East Conflict
cybersecurity researchers have reported a significant spike in retaliatory cyberattacks following recent military actions in the Middle East. Between February 28...
-
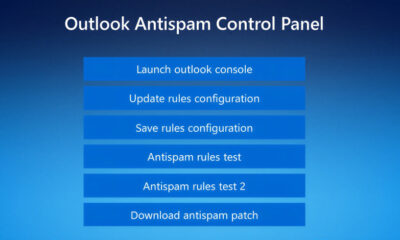

Security
/ 4 weeks agoFake Tech Support Spam Deploys Havoc C2 in New Campaign
Security researchers have identified a new campaign where threat actors are impersonating IT support staff to deploy a powerful command-and-control framework...
-

Security
/ 4 weeks agoSloppyLemming Hackers Target Pakistan, Bangladesh Governments
A cyber threat group known as SloppyLemming has been linked to a new campaign targeting government bodies and critical infrastructure operators...


















