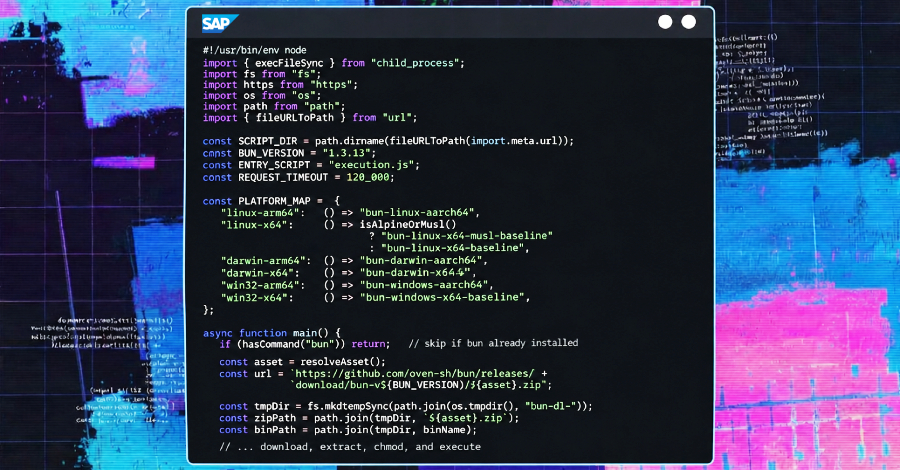
cybersecurity researchers have identified a new supply chain attack campaign that is targeting SAP related npm packages with malware designed to steal credentials. The operation has compromised several widely used JavaScript and cloud application packages, raising concerns about the security of software development pipelines.
According to reports from security firms Aikido Security, SafeDep, Socket, StepSecurity, and Google owned Wiz, the malicious actors behind the campaign have labeled it “mini Shai-Hulud.” The attack involves the compromise of specific npm packages that are associated with SAP’s development ecosystem. The goal of the campaign is to inject credential stealing malware into the software supply chain, potentially affecting developers and organizations that rely on these components.
Scope of the Compromise
The affected packages are part of SAP’s JavaScript and cloud application frameworks. Researchers have confirmed that the compromised versions were published to the public npm registry, making them available for download by unsuspecting developers. The malware embedded within these packages is capable of exfiltrating sensitive information, including login credentials and environment variables, from infected systems.
The campaign has been described as a sophisticated and targeted attack on the software supply chain. By poisoning packages that are directly related to SAP’s application development tools, the attackers aim to gain access to internal corporate networks and cloud infrastructure. The use of the “mini Shai-Hulud” moniker suggests a deliberate effort to brand the operation, potentially linking it to previous or ongoing campaigns.
Security Community Response
Multiple security organizations have issued alerts regarding the compromised packages. Aikido Security, SafeDep, and Socket have all published technical analyses detailing the attack vectors and the specific payloads involved. StepSecurity and Wiz have contributed additional data on the scope and potential impact of the breach.
Industry experts have noted that supply chain attacks continue to be one of the most effective methods for compromising large numbers of downstream users. The targeting of SAP related packages is particularly concerning given the widespread adoption of SAP’s cloud and enterprise software across many industries, including finance, manufacturing, and logistics. A successful breach could provide attackers with a foothold into critical business systems.
Implications for Developers and Organizations
Developers who have used any of the compromised npm packages are advised to immediately audit their projects and verify the integrity of their dependencies. Security teams should review application logs for signs of unauthorized access or data exfiltration. The incident highlights the ongoing risks associated with using open source components without rigorous security checks.
Organizations that rely on SAP’s cloud application platform should take proactive measures to assess their exposure. This includes scanning for known malicious package versions and implementing stricter controls on software supply chain integrity. The attack serves as a reminder that even trusted development ecosystems can be vulnerable to targeted compromise.
Future Outlook and Preventive Measures
The security firms involved in the discovery have notified npm maintainers and SAP regarding the compromised packages. Efforts are underway to remove the malicious versions from the registry and to release patched updates. It is expected that the incident will prompt a broader review of security practices within the npm ecosystem and among SAP development tool users.
Long term solutions may include greater adoption of software bill of materials (SBOM) standards and automated dependency scanning as part of continuous integration pipelines. The incident underscores the necessity for a zero trust approach to software supply chains, where no component is assumed to be secure without continuous verification.
Source: Delimiter Online