A major financial institution’s website was found to have transmitted data from logged-in user sessions to the e-commerce platform Temu, via an advertising pixel from the content recommendation company Taboola. The incident, which occurred without the bank’s or its customers’ knowledge, highlights a significant blind spot in digital security practices surrounding third-party web scripts.
The redirection happened after the bank approved the integration of a standard Taboola advertising pixel on its website. This pixel, designed to track user behavior for ad targeting, was configured to send session data to a tracking endpoint owned by Temu. Security researchers reported that the data transfer took place while users were actively logged into their online banking portals.
How the Data Transfer Occurred
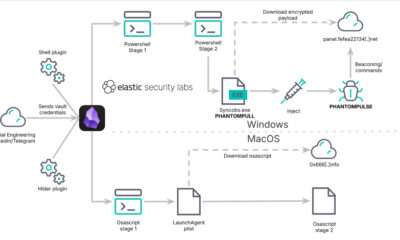
The mechanism exploited a common web tracking technique. When a user visited a page containing the Taboola pixel, the script executed and forwarded information to a server. In this case, the receiving server was linked to Temu’s advertising infrastructure. The pixel operated silently in the background, and the data flow was not detected by the bank’s own security monitoring systems, which failed to register the event as a policy violation.
This type of incident points to a vulnerability often overlooked by security teams, sometimes called the “first-hop bias.” Organizations frequently focus their security controls on the final destination of data, while paying less attention to the initial transfer point to a third-party service. A script from a trusted vendor like Taboola is often assumed to be safe, creating a potential gateway for data to be sent onward to other, less scrutinized parties.
Security and Privacy Implications
The incident raises immediate questions about data privacy and security. While the exact nature of the data transmitted has not been publicly detailed, a logged-in banking session could potentially expose sensitive information. This includes user identifiers, session tokens, device information, and details about the pages a user is viewing within the secure banking environment.
Such data could be used to build detailed profiles of individuals’ financial behaviors or, in a worst-case scenario, could be leveraged in targeted phishing attacks. The transfer occurred without explicit user consent, conflicting with growing global data protection regulations like the GDPR and CCPA, which mandate transparency and user control over personal information.
Reaction and Broader Industry Concern
Security analysts have expressed concern over the widespread nature of this risk. Thousands of websites integrate third-party pixels and scripts for advertising, analytics, and social media functions. Each integration represents a potential vector for unintended data leakage, especially when vendor relationships involve complex sub-processor networks where data can be passed along a chain.
The bank involved has not been officially named in public reports. It is standard procedure in such disclosures to allow the affected organization time to investigate and remediate the issue before its identity is revealed. Taboola and Temu have not issued public statements regarding this specific incident.
Next Steps and Expected Developments
Following the technical disclosure, the affected bank is likely conducting a full audit of all third-party scripts and pixels on its digital properties. The broader financial industry and other sectors handling sensitive data are expected to re-evaluate their vendor risk management programs, with a specific focus on the data flow permissions granted to third-party marketing tools. Regulatory bodies may also scrutinize the incident to determine if any privacy laws were breached, which could lead to investigations or fines. The outcome will depend on the specific data transmitted and the jurisdictional regulations that apply.
Source: Security Intelligence Brief