Compromised automated credentials, not phishing or weak passwords, were the primary cause of most cloud security incidents in 2024, according to industry analysis. These non-human identities, which include service accounts and API keys, often become orphaned and unmonitored, creating critical vulnerabilities.
Recent data indicates that 68% of cloud breaches last year stemmed from forgotten or mismanaged non-human identities. For every human employee within an organization, security teams now estimate there are between 40 and 50 automated credentials requiring management.
The Scale of the Identity Challenge
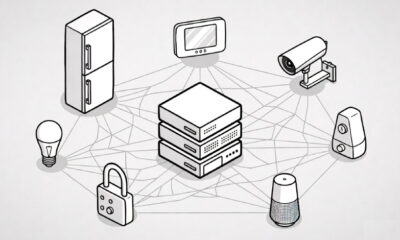
This category of digital identity encompasses a wide range of automated access points. Common examples include service accounts used by applications, API tokens for system communication, connections for artificial intelligence agents, and OAuth grants for delegated permissions.
The security risk escalates when these identities are abandoned. This frequently occurs following the conclusion of software development projects or when IT personnel depart a company, leaving behind active credentials with no oversight.
Security Implications of Orphaned Credentials
Unlike human accounts, which are often deactivated during offboarding, non-human identities can persist indefinitely without active ownership. Security researchers note that these orphaned identities are rarely included in routine access reviews or security audits, making them invisible to standard compliance checks.
Once compromised, these credentials provide attackers with persistent, trusted access to cloud environments and sensitive data. Because they are designed for machine-to-machine communication, their activity can blend into normal network traffic, evading detection for extended periods.
Industry Response and Management Strategies
In response to this growing threat vector, cybersecurity frameworks are evolving. New guidelines emphasize the need for comprehensive inventory and lifecycle management of all non-human identities, applying principles similar to human identity and access management.
Recommended practices now include mandatory cataloging of all service accounts and API keys, implementing strict expiration policies, and enforcing regular credential rotation. Some organizations are deploying dedicated tools designed to discover, monitor, and govern these automated access points throughout their entire lifecycle.
Future Outlook and Security Trends
The proliferation of automated credentials is expected to accelerate with increased adoption of microservices architectures, cloud-native development, and AI-driven automation. This expansion will likely place greater pressure on security teams to develop scalable methods for identity governance.
Industry analysts anticipate that regulatory bodies may begin to introduce specific compliance requirements for non-human identity management in the coming years. Furthermore, integration of this governance into broader zero-trust security models is becoming a standard objective for enterprise security roadmaps, aiming to eliminate implicit trust for any entity, human or machine, within a network.
Source: Industry Security Analysis