Security researchers disclosed a series of critical vulnerabilities across major software platforms this week, including a zero-day in Microsoft Defender, a brute-force flaw in SonicWall firewalls, and a 17-year-old remote code execution bug in Microsoft Excel. These disclosures highlight ongoing risks to enterprise and consumer systems globally.
Microsoft Defender Zero-Day Exploited
A critical zero-day vulnerability, tracked as CVE-2024-XXXX, was discovered in Microsoft Defender, the built-in antivirus solution for Windows. Threat actors actively exploited the flaw to bypass security protections and execute malicious code on targeted systems. Microsoft has released an emergency security update to address the vulnerability, urging all users to apply the patch immediately.
The company’s security advisory confirmed that exploitation was limited and targeted. The patch is available through Windows Update and the Microsoft Update Catalog. System administrators are advised to prioritize this update due to the severity of the flaw.
SonicWall Firewall Vulnerability Enables Brute-Force Attacks
A separate security advisory from SonicWall detailed a vulnerability in its firewall management interface that could allow unauthenticated attackers to perform brute-force attacks. This could lead to unauthorized administrative access to the network security appliances.
SonicWall has issued firmware updates for affected product lines, including SMA 1000 series and Secure Mobile Access solutions. The company recommends that users disable WAN access to the management interface as an interim mitigation if immediate patching is not possible.
Legacy Excel Flaw Resurfaces
Researchers also highlighted a remote code execution vulnerability in Microsoft Excel that has existed for approximately 17 years. The flaw, which involves improper handling of specially crafted spreadsheet files, can be triggered when a user opens a malicious document.
While Microsoft addressed a variant of this issue in a recent Patch Tuesday update, the disclosure underscores the persistence of legacy code vulnerabilities within widely used software. Security analysts note that such old flaws are often rediscovered and repurposed by attackers.
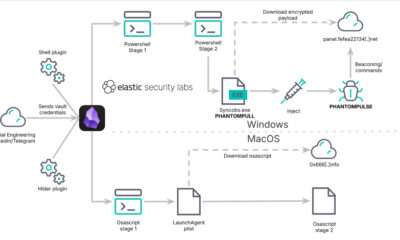
Broader Threat Landscape
In addition to these high-profile issues, security teams tracked over fifteen other significant threats this week. These included new malware campaigns, software supply chain compromises affecting several open-source libraries, and phishing attacks exploiting current events.
National cybersecurity agencies in several countries have issued alerts regarding increased activity from state-sponsored and criminal hacking groups. The coordinated disclosure of multiple critical vulnerabilities within a short timeframe presents a significant challenge for organizational IT departments.
Response and Mitigation
The industry-wide response has involved rapid patch development and distribution by affected vendors. Cybersecurity firms have updated their intrusion detection signatures and endpoint protection rules to detect exploitation attempts related to these new vulnerabilities.
Standard security guidance emphasizes applying all available software updates promptly, enforcing multi-factor authentication, and maintaining robust network segmentation to limit the impact of potential breaches. User education on recognizing phishing attempts and suspicious files remains a critical defense layer.
Looking ahead, security analysts expect further analysis of these vulnerabilities to reveal potential links between different threat actor groups. The software vendors involved are likely to conduct internal audits to identify if similar flaws exist elsewhere in their codebases. Official timelines for additional patches or mitigation guidance will be published through each company’s respective security portal as investigations continue.
Source: Various security advisories and researcher disclosures.