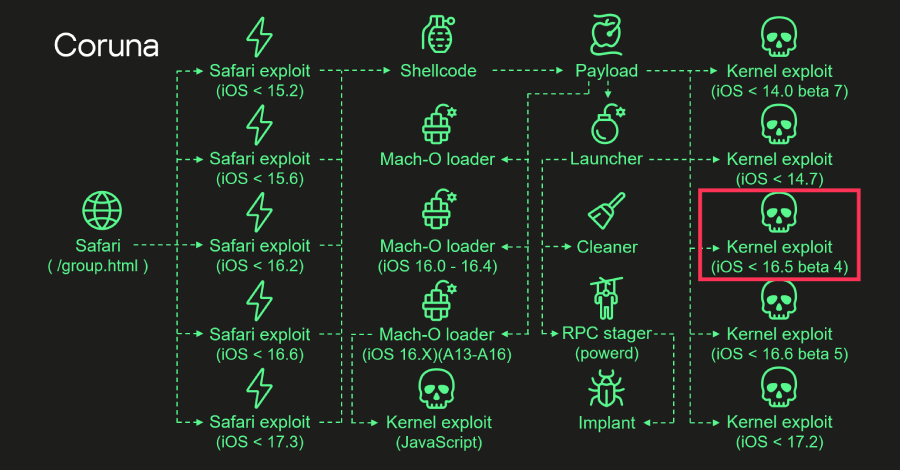
Security researchers have uncovered a direct link between a recently discovered Apple iOS exploit kit and a major cyber-espionage campaign from the previous year. The kernel-level exploit code used in attacks by the “Coruna” kit is an updated version of the same code deployed during the 2023 Operation Triangulation campaign, according to new analysis from cybersecurity firm Kaspersky.
Connecting the Code to Past Campaigns
When the Coruna exploit kit was first reported, public evidence was insufficient to conclusively link its underlying code to the earlier Triangulation operation. Kaspersky’s latest technical investigation has now bridged that gap. The firm’s researchers found that the exploit targeting two specific iOS kernel vulnerabilities is not merely similar; it is a refined iteration of the 2023 code.
This discovery indicates that the developers behind the sophisticated Triangulation attacks have either continued their activities or that their proprietary exploit tools have been repurposed by another threat actor. The reuse of such advanced code underscores a trend where successful cyber-espionage tools are maintained and adapted for new campaigns over time.
Technical Background and Implications
Operation Triangulation, disclosed in mid-2023, was a complex campaign that used a chain of zero-day vulnerabilities to install spyware on iPhones. The attack sequence began with a malicious iMessage attachment that did not require user interaction, leading to full device compromise. The kernel exploit was a critical component of this attack chain, allowing the attackers to break out of the iOS security sandbox.
The Coruna kit, identified in more recent mass-attack attempts, leverages this same core exploit mechanism, albeit with modifications. These updates likely aim to bypass security patches Apple released following the disclosure of the original vulnerabilities. The kit’s purpose appears to be the silent installation of spyware or other malicious payloads on compromised devices.
Industry and Vendor Response
The cybersecurity community has emphasized the significance of this code reuse. It demonstrates that high-value exploit code, once developed, becomes a persistent asset in the threat landscape. Security teams now must consider that patched vulnerabilities may still be targeted by evolved exploits that work around the fixes.
Apple has previously addressed the vulnerabilities exploited in the Triangulation campaign through security updates. The company routinely advises users to keep their devices updated to the latest version of iOS to protect against known threats. The discovery of Coruna highlights the ongoing cat-and-mouse game between platform security teams and advanced persistent threat (APT) groups.
Looking Ahead: Next Steps for Security
Kaspersky’s report is expected to lead to further analysis by other security vendors, who will scan for indicators of compromise related to the updated Coruna kit. Organizations and individuals are advised to ensure all Apple devices are running the most current iOS version available. Researchers will continue to monitor for any new variants of this exploit kit or related activity, as the group behind it remains active. The linkage between campaigns across years suggests that defenders must prepare for the long-term lifecycle of advanced cyber weapons.
Source: Kaspersky