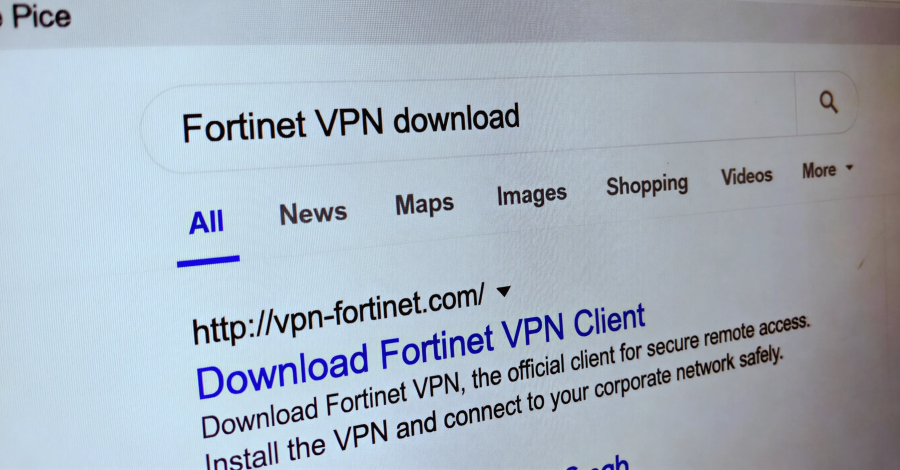
Microsoft has disclosed details of an ongoing cybercrime campaign that uses search engine optimization (SEO) poisoning to distribute fake virtual private network (VPN) clients designed to steal user credentials. The campaign, attributed to a threat actor tracked as Storm-2561, redirects individuals searching for legitimate business software to malicious websites hosting trojan-infected downloads.
Campaign Mechanics and Infection Chain
The operation begins when users search for popular enterprise software or tools online. Attackers use SEO poisoning techniques to ensure their malicious websites appear high in search results for these queries. When a user clicks on one of these links, they are taken to a site that hosts a digitally signed trojan disguised as a VPN client installer, often contained within a ZIP archive file.
These trojans are crafted to mimic trusted VPN applications from reputable companies. Once executed on a victim’s system, the malicious software establishes a backdoor. This allows the attackers to harvest sensitive information, including usernames, passwords, and other authentication credentials stored in the browser or system memory.
Technical Analysis and Attribution
Microsoft’s security researchers identified the campaign’s infrastructure and tactics, linking the activity to the Storm-2561 group. The use of digital signatures on the malicious files is a notable aspect of the attack, as it helps the trojans evade basic security checks and appear legitimate to both users and some automated detection systems.
The threat actor employs a multi-stage process to deploy the final payload. The initial downloader is responsible for fetching and executing additional components from attacker-controlled servers. This modular approach makes the malware more adaptable and harder for static security solutions to detect in full.
Broader Implications for Enterprise Security
This campaign highlights a significant shift in cybercriminal tactics, moving beyond simple phishing emails to exploit the trust users place in search engines. The targeting of individuals seeking business software suggests the threat actor is primarily interested in compromising corporate networks and stealing enterprise credentials.
Security experts note that such attacks pose a substantial risk to organizations, as stolen VPN credentials can provide attackers with a direct pathway into internal corporate networks. This access can lead to data theft, ransomware deployment, or espionage activities.
Recommended Protective Measures
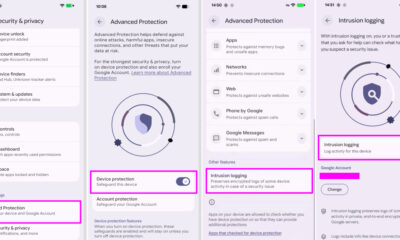
Microsoft and other security firms advise both organizations and individual users to exercise heightened caution when downloading software from the web. Recommendations include verifying the authenticity of download sources by visiting official vendor websites directly, rather than relying on search engine links for critical software.
Organizations are encouraged to implement application allowlisting policies, deploy endpoint detection and response (EDR) solutions, and ensure all software is kept updated with the latest security patches. User awareness training focusing on digital hygiene and recognizing potentially malicious sites remains a critical defense layer.
Microsoft has reported that its Defender antivirus and other security products have been updated to detect and block the known malware associated with this campaign. The company continues to monitor Storm-2561’s activities and is collaborating with industry partners to take down the malicious infrastructure used in these attacks. Further technical indicators of compromise are expected to be shared with the wider security community to bolster collective defense efforts.
Source: Microsoft Security Blog