Security researchers have identified a series of significant cyber threats and vulnerabilities over the past week, highlighting risks to authentication systems, endpoint security tools, and popular communication platforms. The findings, compiled in a weekly threat intelligence bulletin, detail methods that could be exploited in real-world attacks against organizations and individuals globally.
OAuth Implementation Flaws and Phishing Campaigns
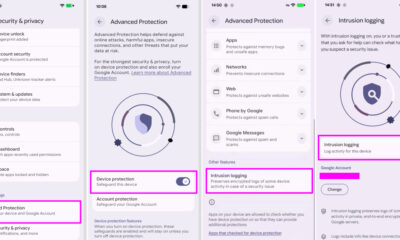
One prominent threat involves the misuse of OAuth, a standard protocol for authorization. Attackers are crafting malicious OAuth applications designed to appear legitimate. If a user grants permissions to such an application, it can gain persistent access to the user’s data without requiring their password again. This technique bypasses multi-factor authentication and can lead to long-term account compromise.
Separately, a sophisticated phishing campaign has been targeting users of the encrypted messaging service Signal. The attack involves fraudulent notifications that mimic official Signal alerts, attempting to trick users into revealing their account credentials or verification codes.
Vulnerabilities in Security Software and File Archives
New research has demonstrated methods to disable or bypass Endpoint Detection and Response (EDR) systems, which are critical security tools for monitoring and responding to threats on computers and servers. The techniques highlight potential weaknesses in the defensive software itself, which could allow attackers to operate undetected on a compromised network.
Another reported threat involves a novel attack method dubbed “Zombie ZIP.” This exploit manipulates ZIP archive files in a way that can cause significant performance issues or denial-of-service conditions when the archive is scanned by security software or extracted by a system. The attack leverages the complex structure of archive files to consume excessive system resources.
Compromise of AI and Machine Learning Platforms
Further research has uncovered vulnerabilities within platforms used for developing and deploying artificial intelligence and machine learning models. While specific details are often withheld to prevent immediate exploitation, the general class of vulnerabilities could allow unauthorized access to sensitive training data, model intellectual property, or computational resources.
Security analysts note a trend where established attack methods are being refined and combined with new research to create more potent threats. This continuous evolution requires constant vigilance from both security vendors and organizational IT departments.
Industry Response and Mitigation Steps
In response to these disclosures, major technology and security firms typically issue patches, update detection rules, and publish security advisories. Organizations are advised to ensure all software, especially security tools and development platforms, is promptly updated to the latest versions.
Security experts recommend reviewing and auditing OAuth applications connected to corporate and personal accounts, removing any that are unused or unrecognized. User awareness training is also emphasized as a key defense against sophisticated phishing attempts, even those targeting platforms known for strong encryption.
Looking forward, the cybersecurity community anticipates that the techniques described in this week’s research will likely be integrated into active attack campaigns. Continued monitoring of threat intelligence feeds and adherence to foundational security practices, such as the principle of least privilege and robust backup strategies, are considered essential for defense.
Source: Various security research publications and threat intelligence bulletins.