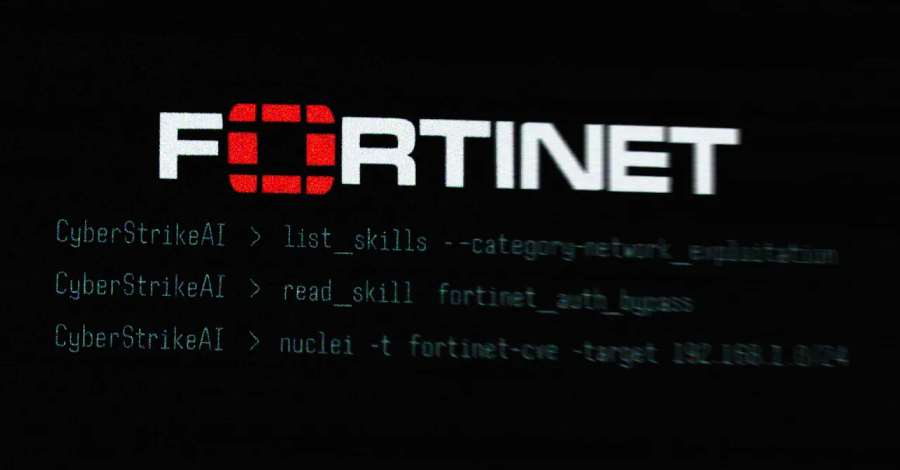
Security researchers have identified the use of an open-source, artificial intelligence-powered platform in a widespread campaign targeting network security appliances across at least 55 countries. The threat actor behind the attacks leveraged a tool called CyberStrikeAI to exploit vulnerabilities in Fortinet FortiGate firewalls, according to a new report from cybersecurity firm Team Cymru.
Scope and Discovery of the Campaign
The investigation began with the analysis of a specific IP address, 212.11.64[.]250, which was linked to the malicious activity. Team Cymru’s analysis traced connections from this address to numerous compromised FortiGate devices globally. The campaign’s geographic spread indicates a significant, coordinated effort to breach corporate and organizational networks.
FortiGate appliances are widely used by enterprises to secure their network perimeters. A successful compromise of such a device can provide attackers with a deep foothold inside a victim’s network, allowing for data theft, espionage, or further lateral movement.
The Role of CyberStrikeAI
The operation is notable for its use of CyberStrikeAI, a publicly available security testing platform built with AI-native capabilities. This marks a concerning evolution in the tools available to threat actors. The platform is designed to automate and enhance various penetration testing tasks, and its open-source nature makes it easily accessible.
By utilizing this AI-assisted tool, the attackers could potentially automate the process of identifying vulnerable systems, crafting exploits, and executing attacks with greater speed and scale. The use of such a tool lowers the technical barrier for conducting sophisticated campaigns.
Industry and Official Response
Fortinet has previously issued advisories and patches for the vulnerabilities believed to be exploited in these attacks. The company consistently recommends that customers apply security updates promptly to mitigate known risks. Team Cymru has shared its findings with relevant cybersecurity authorities and Computer Emergency Response Teams (CERTs) in affected regions.
Security experts emphasize that the weaponization of open-source AI tools represents a new challenge for defenders. It underscores the dual-use nature of many security technologies, which can be employed for both defensive research and offensive operations.
Looking Ahead: Mitigation and Vigilance
The disclosure of this campaign is expected to prompt renewed warnings from global cybersecurity agencies. Organizations using Fortinet products are urged to verify they are running the latest firmware versions and to review their systems for any signs of compromise linked to the identified indicators. Further analysis of the CyberStrikeAI platform’s use in the wild is likely, as security firms dissect the attack methodology to improve detection rules. The incident sets a precedent that will likely influence how the security community monitors the development and application of open-source AI security tools.
Source: Team Cymru