Chief Information Security Officers globally are confronting a fundamental structural challenge within their Security Operations Centers, according to industry analysis. The frontline personnel responsible for initial threat detection often possess the least experience, creating a vulnerability that can degrade security performance over time. This situation presents a direct risk to organizational cybersecurity posture.
The Frontline Analyst Dilemma
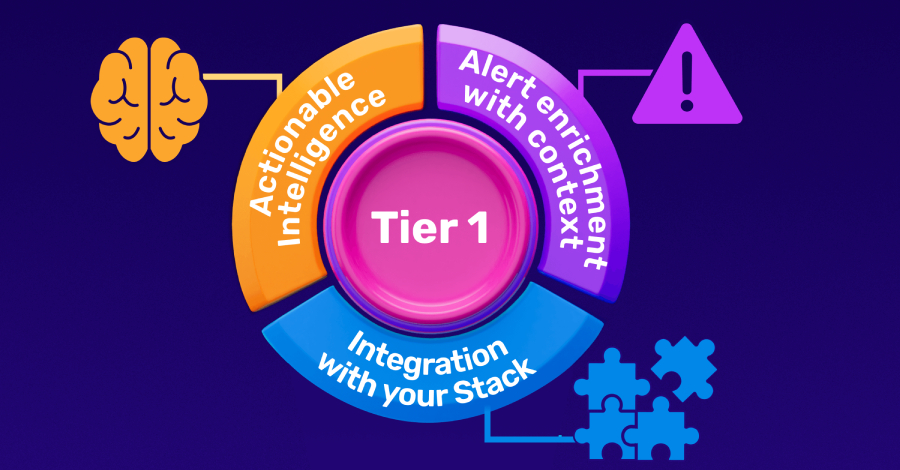
Tier 1 security analysts form the first line of defense in most modern Security Operations Centers. Their primary duty involves monitoring alerts and identifying potential security incidents in real time. However, these positions are frequently staffed by junior personnel early in their cybersecurity careers.
This staffing model creates a significant operational paradox. The individuals tasked with the critical, time-sensitive job of initial threat recognition are simultaneously those with the most limited practical exposure to complex attack patterns. Industry observers note this gap between responsibility and experience is a persistent issue.
Pressures Eroding SOC Performance
Beyond the experience gap, Tier 1 teams face considerable cognitive and organizational pressures. The role requires sustained concentration while sifting through high volumes of security alerts, many of which are false positives. This environment can lead to alert fatigue, a well-documented phenomenon where analysts become desensitized to notifications.
Organizational factors, including shift work, high turnover rates, and sometimes unclear escalation procedures, further compound these cognitive demands. These combined pressures can quietly erode the overall effectiveness and efficiency of a security operations center if not systematically addressed.
The Path Forward for Security Leadership
For CISOs, addressing this frontline vulnerability is now a recognized priority. The focus has shifted from simply filling seats to strategically building a high-impact Tier 1 function. This involves a multi-step approach centered on enhancing analyst capability and resilience.
The first step involves re-evaluating the tools and interfaces provided to junior analysts. Simplifying console views and automating routine triage tasks can reduce cognitive load, allowing analysts to focus on genuine threats. The second step requires investing in continuous, scenario-based training that goes beyond initial certification.
The third critical step is structural, focusing on career pathing and support. Creating clear escalation pathways to Tier 2 and Tier 3 experts, alongside implementing robust mentorship programs, can improve retention and build institutional knowledge. This approach aims to transform the Tier 1 role from a temporary stop into a foundational career stage.
Industry Implications and Next Steps
The discussion around Tier 1 effectiveness is part of a broader industry conversation about cybersecurity talent management and operational resilience. As attack volumes and sophistication increase, the efficiency of the initial detection layer becomes more crucial.
Moving forward, industry groups and enterprise security leaders are expected to publish further guidelines and best practices for SOC structuring. The development of more intuitive security platforms with integrated analyst assistance is also anticipated. The overarching goal remains building sustainable security operations that can withstand both technical threats and internal organizational pressures.
Source: Industry Analysis