cybersecurity researchers have disclosed a new botnet loader that uses a public blockchain to store its commands, creating a resilient infrastructure that is difficult for authorities to disrupt. The discovery, made by security firm Qrator Labs, highlights an evolving tactic among cybercriminals seeking to leverage decentralized technology for malicious purposes.
Aeternum C2’s Blockchain-Based Infrastructure
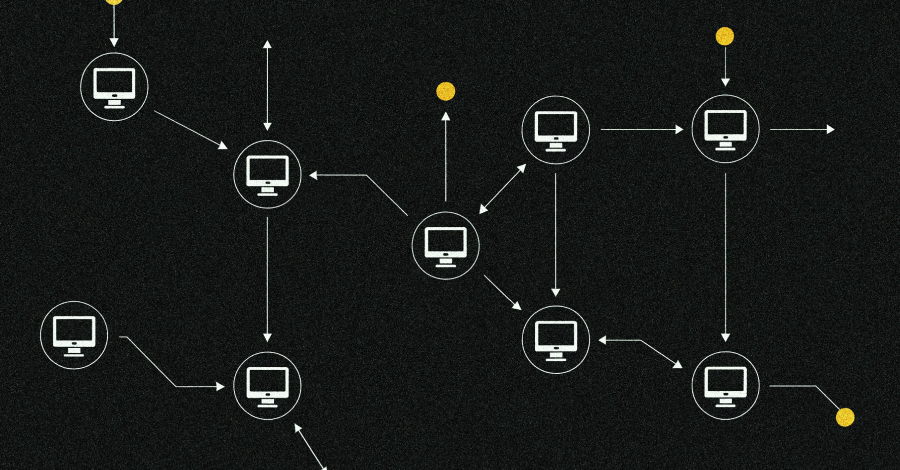
The botnet, named Aeternum C2, operates by storing its command-and-control (C2) instructions directly on the Polygon blockchain. This method represents a significant shift from traditional botnet architectures, which typically rely on centralized servers or domains that can be seized or shut down by law enforcement and cybersecurity firms.
According to the report from Qrator Labs, the botnet’s operators encode their commands into blockchain transactions. Infected devices then scan the public Polygon ledger for these specific, encrypted instructions. This approach makes the command chain highly persistent and resistant to conventional takedown efforts, as the data exists on a distributed, immutable network.
How the Botnet Operates
Aeternum functions as a loader, a type of malware designed to deploy additional payloads onto a compromised system. Once a device is infected, it connects to the blockchain to retrieve encrypted commands from the attackers. These commands can instruct the botnet to download more dangerous malware, such as ransomware or information stealers.
The use of the Polygon network is strategic; it is a popular blockchain known for lower transaction fees compared to Ethereum, its parent chain. This makes it a cost-effective platform for attackers to operate their C2 infrastructure continuously without significant financial overhead.
Implications for Cybersecurity
This development signals a growing trend of malware authors incorporating legitimate decentralized technologies into their attack frameworks. Blockchain’s core attributes of transparency and immutability, while beneficial for many applications, present a unique challenge when exploited for criminal coordination.
Security experts note that this method complicates defensive measures. While a traditional C2 server can be taken offline through coordination with hosting providers, data stored on a public blockchain cannot be easily erased. Defenders must instead focus on detecting the malicious transactions themselves or preventing the initial infection and the malware’s ability to read the chain.
Industry and Researcher Response
The disclosure by Qrator Labs has been shared with broader cybersecurity communities and relevant authorities. The firm’s report provides technical indicators of compromise (IOCs) that other security teams can use to hunt for the botnet within their networks.
Responses from the cybersecurity industry suggest an increased focus on behavioral detection and network monitoring for unusual blockchain traffic from endpoints. The fundamental shift requires adapting defensive strategies to counter infrastructure that can no longer be “sunkholed” or seized in a traditional sense.
Looking Ahead
Security analysts anticipate that other threat actors will likely adopt and refine similar blockchain-based C2 techniques following this revelation. The ongoing cat-and-mouse game between cybercriminals and defenders is entering a new phase involving decentralized web3 technologies. Future defensive research is expected to concentrate on advanced methods for identifying malicious smart contracts and blockchain transactions, as well as enhancing endpoint security to block the initial loader infections before they can retrieve commands.
Source: Qrator Labs Report