A sophisticated Chinese cyber espionage group has been linked to a multi-year campaign targeting critical infrastructure organizations across Asia. The attacks, which began several years ago and are ongoing, have focused on high-value entities in the aviation, energy, government, and telecommunications sectors.
Security researchers from Palo Alto Networks Unit 42 have attributed the activity to a previously undocumented threat group. The campaign’s primary goal appears to be intelligence gathering and long-term access to sensitive networks.
Attack Methodology and Tools
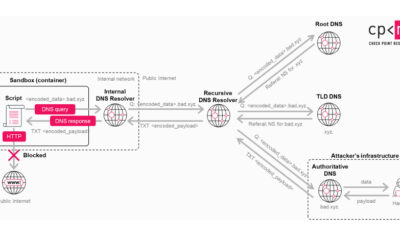
The threat actors employ a multi-stage approach to breach target networks. Initial access is frequently gained by exploiting vulnerabilities in public-facing web servers and applications. Once inside, the attackers deploy a range of tools to move laterally, escalate privileges, and steal credentials.
A key tool in their arsenal is Mimikatz, an open-source application used to harvest login credentials from a computer’s memory. The use of Mimikatz allows the group to obtain high-level administrative passwords, enabling them to access secured parts of the network and maintain persistence.
Geographic and Sectoral Focus
The campaign has shown a clear geographic concentration, with victims identified in South, Southeast, and East Asia. Beyond critical infrastructure, the threat group has also targeted organizations in law enforcement, the pharmaceutical industry, and the technology sector.
This broad targeting suggests a strategic interest in obtaining geopolitical, economic, and technical intelligence from across the region. The long duration of the campaign indicates a patient, resource-backed operation focused on stealth and continuous data collection.
Attribution and Industry Response
While Palo Alto Networks Unit 42 has attributed the activity to a China-nexus actor, they have not publicly named a specific group or directly linked it to the Chinese government. The tactics, techniques, and procedures, however, align with those commonly associated with state-sponsored espionage actors based in China.
In response to these findings, cybersecurity firms are urging organizations in the affected regions and sectors to review their external web assets. Prioritizing the patching of web server and application vulnerabilities is considered a critical first step in defense.
Network defenders are also advised to monitor for signs of credential dumping tools like Mimikatz and to implement strong credential hygiene, including the use of multi-factor authentication and regular password rotation for privileged accounts.
Ongoing Investigations and Future Outlook
International cybersecurity agencies are likely reviewing the disclosed intelligence to determine overlaps with known threat clusters. Further technical indicators of compromise are expected to be shared with the global security community to aid in detection efforts.
Given the campaign’s persistence and strategic targets, security analysts anticipate that the threat group will continue its operations, potentially refining its tools and expanding its target list. Organizations are advised to treat this disclosure as a actionable warning to bolster their defensive postures against advanced persistent threats.
Source: Palo Alto Networks Unit 42