cybersecurity researchers have uncovered a sophisticated, multi-stage malware operation that uses obfuscated batch scripts to deploy a suite of dangerous remote access trojans, including XWorm, AsyncRAT, and Xeno RAT. The campaign, identified by Securonix Threat Research under the codename VOID#GEIST, represents a significant threat due to its stealthy delivery method and the powerful, encrypted payloads it ultimately installs on victim systems.
The Attack Chain and Technical Details
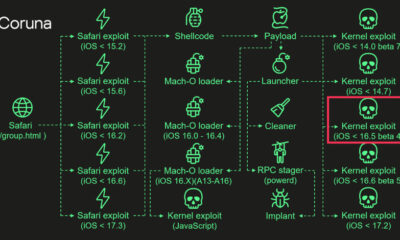
The attack begins with a heavily obfuscated batch script. This initial script is designed to evade basic detection and analysis. Its primary function is to retrieve and execute a second, more complex stage of the attack from a remote command and control server controlled by the threat actors. This layered approach allows the attackers to keep their core malicious code off the initial delivery vehicle, making analysis more difficult for security software.
The secondary payload delivered by the script is a collection of encrypted remote access trojan (RAT) executables. RATs are a particularly dangerous form of malware that grants attackers full control over an infected computer. Once decrypted and executed, these RATs correspond to known families: XWorm, AsyncRAT, and Xeno RAT. Each of these malware families provides attackers with capabilities for data theft, surveillance, and further system compromise.
Capabilities of the Delivered Malware
The final payloads enable a wide range of malicious activities. XWorm is known for features like keylogging, cryptocurrency wallet theft, and the ability to spread via removable USB drives. AsyncRAT is an open-source RAT that allows for remote desktop control, file management, and executing commands. Xeno RAT, another powerful tool, provides similar remote access and data exfiltration functionalities. The combination of these tools in a single campaign suggests the attackers are seeking comprehensive access to victim networks for espionage or financial gain.
The use of batch scripts as an initial vector is notable for its simplicity and effectiveness. While often overlooked, batch files can be powerful tools for automating complex sequences of commands, including downloading and running other programs. The obfuscation techniques employed make the script’s intentions unclear to both human reviewers and some automated security systems until it is too late.
Broader Implications and Defense
The VOID#GEIST campaign highlights an ongoing trend where threat actors use living-off-the-land techniques, leveraging legitimate system tools like batch scripts to fly under the radar. This method bypasses traditional security measures that might only scan for known malicious executable files. The campaign’s global targeting means organizations and individuals worldwide are potential victims.
Security experts recommend several defensive measures. These include exercising caution with email attachments and links from unknown sources, as these are common delivery methods for initial scripts. Organizations should also implement application allowlisting to prevent unauthorized scripts from running and employ advanced endpoint detection and response (EDR) solutions that can analyze script behavior for malicious intent, not just static file signatures.
Researchers at Securonix continue to monitor the infrastructure associated with VOID#GEIST. The cybersecurity community expects the threat actors behind this campaign to update their tactics and infrastructure in response to public disclosure. Network defenders are advised to review their logs for indicators of compromise associated with this attack chain and ensure their security systems are updated to detect the described behaviors.
Source: Securonix Threat Research