A North Korean state-sponsored hacking group is suspected of orchestrating a sophisticated cloud compromise against a cryptocurrency organization in 2025, resulting in the theft of millions of dollars in digital assets. The intrusion is believed to have begun when a developer at the targeted firm inadvertently installed a malicious file received via Apple’s AirDrop feature on a work device.
The threat actor, tracked by cybersecurity researchers as UNC4899, employed a multi-stage attack to infiltrate the company’s cloud infrastructure. Security analysts attribute the campaign with moderate confidence to the North Korean regime. The group is also known by other identifiers, including Jade Sleet, PUKCHONG, and Slow Pisces.
Attack Vector and Initial Compromise
The breach reportedly started with a social engineering tactic. A developer within the cryptocurrency organization received a file via AirDrop, a wireless file-sharing service native to Apple devices. Believing the file to be legitimate, the developer opened it on a corporate machine.
This file was a trojanized application, meaning it appeared harmless but contained hidden malicious code. Once executed, the file deployed malware that established a foothold on the developer’s system. This initial access then allowed the attackers to move laterally through the corporate network.
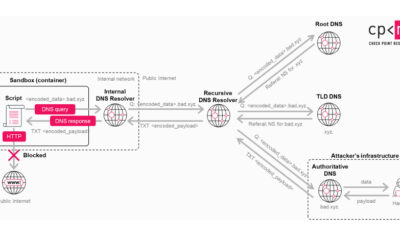
Escalation to Cloud Infrastructure
After gaining access to the internal network, UNC4899 focused on compromising the company’s cloud environment. The attackers leveraged stolen credentials and exploited misconfigurations to gain elevated privileges within cloud management consoles.
With administrative control over critical cloud services, the threat actors could access and manipulate the firm’s cryptocurrency wallets and transaction systems. This level of access enabled them to siphon off millions of dollars worth of cryptocurrency directly from the organization’s holdings.
Attribution and Historical Context
Cybersecurity firms have linked the tools, techniques, and procedures used in this attack to known North Korean cyber operations. Nation-state groups from North Korea, such as the Lazarus Group, have a long history of targeting cryptocurrency exchanges and fintech companies to fund state activities.
The use of AirDrop as an initial vector is a notable evolution in their methods, demonstrating adaptability in targeting individuals with access to valuable systems. The moderate confidence in attribution stems from technical evidence that overlaps with previous campaigns conducted by these actors.
Security Implications and Recommendations
This incident highlights the persistent threat posed by advanced persistent threat groups to the cryptocurrency sector. It underscores the risks associated with using consumer-grade file-sharing services on corporate devices without strict security policies.
Security experts recommend that organizations in high-risk industries disable wireless sharing protocols like AirDrop on business networks. They also emphasize the need for robust cloud security posture management, including strict identity and access controls, multi-factor authentication, and continuous monitoring for anomalous activity.
Law enforcement and cybersecurity agencies in multiple countries are investigating the breach. The targeted firm is working with forensic specialists to contain the incident and assess the full extent of the financial losses. Future legal actions or sanctions against the responsible entities may follow as the international investigation progresses.
Source: GeekWire