All posts tagged "threat detection"
-


Security
/ 3 days agoSecurity Teams Adapt to Multi-OS Attack Threat
Security operations centers (SOCs) globally are implementing new strategies to counter a rising trend of cyberattacks that simultaneously target multiple operating...
-


Security
/ 1 week agoAttackers Shift to Abusing Trusted IT Tools, Evading Detection
cybersecurity professionals worldwide are reporting a significant shift in the tactics of malicious actors, who are increasingly forgoing traditional malware in...
-


Security
/ 2 weeks agoSecurity Experts Warn of Overconfidence in Cyber Defenses
Security professionals are raising concerns that many organizations may be overestimating the effectiveness of their cybersecurity measures. While security tools are...
-


Security
/ 4 weeks agoCISOs Advised on Scaling Phishing Detection in Security Operations
Security leaders are being urged to reassess their strategies for identifying phishing attacks, as these campaigns increasingly evade traditional security measures....
-

Security
/ 1 month agoCISOs Face Critical Challenge in Building Effective Security Teams
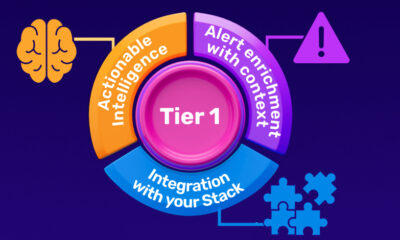
Chief Information Security Officers globally are confronting a fundamental structural challenge within their Security Operations Centers, according to industry analysis. The...
-


Security
/ 2 months agoHands-On NDR Training Provides Insight into Network Security Operations
A recent Hands-On training session with a Network Detection and Response (NDR) platform offered a practical look into the tools and...
-


Artificial Intelligence
/ 2 months agoVega Security Raises $120M Series B Led by Accel
Vega Security has secured $120 million in a Series B funding round, a significant investment that values the cybersecurity firm at...
-


Security
/ 2 months agoOpenClaw Integrates VirusTotal to Scan ClawHub Skills for Security
The automation platform OpenClaw has integrated VirusTotal’s threat intelligence to scan all skills uploaded to its ClawHub marketplace. This partnership, announced...
-


Security
/ 2 months agoEarly Decisions in First 90 Seconds Critical to Incident Response
The initial moments following the detection of a security breach are now widely regarded as the most critical phase of any...

















