All posts tagged "cybersecurity"
-


Security
/ 3 days agoCasbaneiro Phishing Campaign Targets Latin America, Europe
A sophisticated phishing operation is targeting Spanish-speaking users in corporate environments across Latin America and Europe. The campaign delivers the Casbaneiro...
-


Security
/ 3 days agoEnterprise Security Shifts from Blocking to Enabling Tools
A significant cultural shift is underway within enterprise security departments globally, moving away from a default posture of denial toward modern...
-


Security
/ 3 days agoMicrosoft Warns of WhatsApp Malware Targeting Windows
Microsoft has identified a new cyberattack campaign that uses WhatsApp messages to deliver malicious scripts capable of taking control of Windows...
-

Security
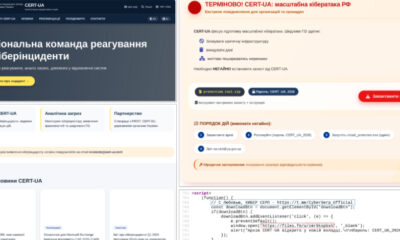
/ 3 days agoCERT-UA Impersonated in Phishing Campaign Spreading AGEWHEEZE Malware
The Computer Emergency Response Team of Ukraine (CERT-UA) has disclosed a widespread phishing campaign in which threat actors impersonated the cybersecurity...
-


Tech News
/ 3 days agoAlleged Messages from Kristi Noem’s Husband Raise Security Concerns
Allegations have surfaced regarding Bryon Noem, the husband of South Dakota Governor Kristi Noem, and his purported involvement in private online...
-


Security
/ 3 days agoGoogle Links Axios npm Attack to North Korean Hackers
Google has formally attributed a recent software supply chain attack to a North Korean state-sponsored hacking group. The attack targeted the...
-


Security
/ 3 days agoAttackers Shift to Abusing Trusted IT Tools, Evading Detection
cybersecurity professionals worldwide are reporting a significant shift in the tactics of malicious actors, who are increasingly forgoing traditional malware in...
-

Artificial Intelligence
/ 3 days agoAI Startup Mercor Hit by Cyberattack via Compromised Open-Source Tool
AI recruiting startup Mercor has confirmed a security incident after a cybercriminal group claimed responsibility for stealing data from the company’s...
-


Security
/ 4 days agoSilver Fox Hackers Target Asia with New RAT and Fake Domains
A sophisticated cyber espionage campaign is actively targeting Chinese-speaking users across Asia, deploying a previously undocumented remote access trojan through counterfeit...
-

Security
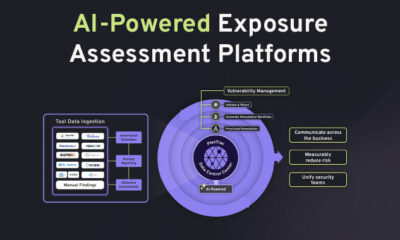
/ 4 days agoAI Arms Race Elevates Cybersecurity to Board Level Priority
The global cybersecurity landscape is undergoing a fundamental shift, driven by the rapid weaponization of artificial intelligence by threat actors. This...

















