cybersecurity researchers have disclosed details of an advanced persistent threat group, dubbed Silver Dragon, which has been linked to cyber attacks targeting government entities in Europe and Southeast Asia since at least mid-2024. The group, which exhibits strong links to the China-nexus threat actor known as APT41, uses sophisticated techniques including the Cobalt Strike penetration testing tool and Google Drive for command and control.
Initial Access and Attack Methods
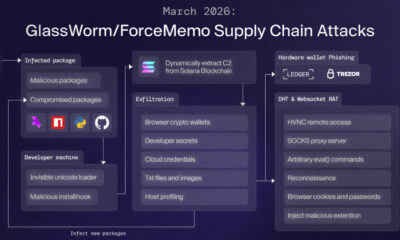
According to a report from cybersecurity firm Check Point, Silver Dragon gains its initial access by exploiting vulnerabilities in public-facing internet servers. The group also delivers phishing emails containing malicious attachments to compromise target networks.
Once inside a system, the attackers deploy a custom backdoor to establish persistence and move laterally. They utilize the legitimate Cobalt Strike framework, a tool often used by security professionals for red team exercises, to conduct post-exploitation activities. This includes credential theft, data exfiltration, and further network reconnaissance.
Use of Legitimate Cloud Services for C2
A notable aspect of this campaign is the group’s use of Google Drive for command and control, or C2, communications. By leveraging this legitimate and widely trusted cloud service, the attackers can blend their malicious traffic with normal web activity, making detection more difficult for network defenders.
This tactic allows Silver Dragon to stealthily receive instructions from its operators and send stolen data back to them without relying on traditional, more easily blocked malicious domains or servers.
Attribution and Links to APT41
Researchers attribute the Silver Dragon activity with high confidence to the APT41 group, also tracked under names like Barium, Winnti, and Double Dragon. APT41 is a prolific Chinese state-sponsored espionage group known for conducting cyber operations for financial gain and intellectual property theft.
The technical overlaps, including code similarities in custom malware and shared infrastructure, provide a strong link between the newly identified Silver Dragon campaigns and the known tactics, techniques, and procedures of APT41.
Targets and Implications
The primary targets of the Silver Dragon campaign are government organizations across Europe and Southeast Asia. The objective appears to be espionage, focusing on the theft of sensitive political, economic, and strategic information.
This activity underscores a continuing trend where state-aligned threat actors are refining their methods to evade detection. The use of dual-use tools like Cobalt Strike and abuse of common cloud platforms presents a significant challenge for traditional security measures.
Recommended Defensive Measures
Security experts recommend several steps to defend against such threats. Organizations should ensure all public-facing applications are promptly patched and implement strong email filtering to block phishing attempts. Monitoring network traffic for anomalous connections to cloud storage services is also advised.
Furthermore, applying the principle of least privilege and segmenting networks can limit an attacker’s ability to move laterally after an initial breach. Security teams are encouraged to hunt for indicators of compromise associated with Cobalt Strike beacons and suspicious Google Drive API activity.
Based on the established pattern of APT41 operations, cybersecurity analysts expect Silver Dragon to continue its espionage campaigns, potentially expanding its target list. The group is likely to further adapt its tools and infrastructure in response to public disclosures and defensive actions taken by potential targets. Continued vigilance and information sharing within the global security community are considered essential to counter this persistent threat.
Source: Check Point Research