Security professionals are raising concerns that many organizations may be overestimating the effectiveness of their cybersecurity measures. While security tools are widely deployed, generating alerts and populating dashboards, the fundamental question of whether these defenses would halt a genuine, sophisticated attack often remains untested and unanswered.
The Illusion of Security
Industry analysis suggests a common pattern where the mere presence of a security control leads to an assumption that it is functioning correctly. Similarly, an active detection rule is frequently expected to perform its task without validation. This assumption, according to experts, creates a dangerous gap between perceived security and actual resilience.
The situation is described as precarious because this gap is typically only revealed during an actual security incident. By that point, the failure of a control or rule can lead to significant data breaches, financial loss, and operational disruption.
The Critical Need for Validation
The core issue identified is a lack of systematic validation. Security teams often operate in an environment where tools are installed and configured, but their efficacy against real-world adversary tactics, techniques, and procedures (TTPs) is not routinely verified. This validation goes beyond checking if a software is running; it involves testing whether it can accurately identify and block malicious behavior as intended.
This process is distinct from standard vulnerability scanning or compliance checking. It requires simulating the actions of determined attackers to challenge the entire defensive ecosystem, from perimeter controls to internal detection and response capabilities.
Moving Beyond Assumptions
Observers note that the cybersecurity industry has historically focused heavily on threat prevention and detection. However, a growing consensus emphasizes that investment in these areas must be matched by equal investment in proving their worth. Without evidence-based validation, security postures are built on a foundation of uncertainty.
This shift in perspective moves the focus from simply having security tools to demonstrably understanding their performance and limitations. It advocates for a more empirical approach to security management, where confidence is derived from test results rather than configuration status.
Implications for Organizational Security
The warning carries significant implications for risk management and strategic planning. Organizations that do not validate their defenses may be misallocating resources, investing in solutions that do not perform as expected while leaving critical vulnerabilities unaddressed. This can create a false sense of security among leadership and stakeholders.
Furthermore, in an evolving regulatory landscape, demonstrating due care in cybersecurity increasingly requires proof of control effectiveness, not just proof of purchase or deployment. Validation exercises can provide crucial evidence for audit and compliance requirements.
Industry Response and Methodology
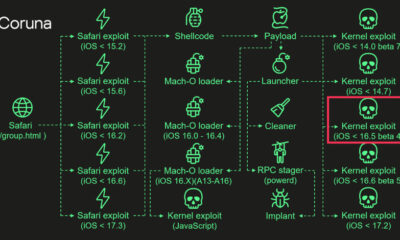
The response within the security community has been a growing advocacy for structured testing methodologies. These include controlled red team exercises, breach and attack simulation (BAS) platforms, and purple teaming, where defensive and offensive security personnel collaborate to test and improve defenses iteratively.
The objective of these methods is to create a continuous feedback loop. Security teams can identify which alerts correlate with real attacks, which rules generate excessive false positives, and where defensive layers have blind spots. This data-driven approach allows for precise tuning of security infrastructure.
Future Outlook for Defense Posture
Looking ahead, the expectation among analysts is that validation will become a non-negotiable component of mature cybersecurity programs. As attack techniques grow more sophisticated, the cost of assuming control effectiveness becomes prohibitively high. The trend is moving toward cybersecurity measures being treated as any other critical business system: their performance must be measured, verified, and reported.
Organizations are anticipated to increasingly integrate regular security control validation into their operational rhythms. This practice is likely to shift from an advanced activity to a standard baseline requirement for any entity seeking to manage its cyber risk credibly in the coming years.
Source: Industry Analysis