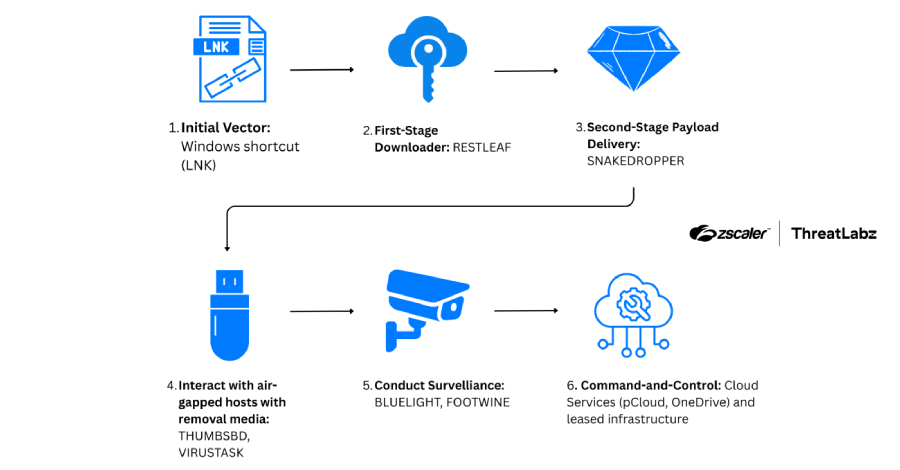
A North Korean state-sponsored hacking group has been observed using a novel combination of cloud-based and physical media malware to infiltrate isolated computer systems. The campaign, attributed to the advanced persistent threat actor known as ScarCruft, employs a backdoor that communicates through the Zoho WorkDrive cloud service and a separate implant designed to spread via USB devices.
The activity, which researchers have codenamed “Ruby Slipper,” was detailed by cybersecurity firm Zscaler ThreatLabz. It represents a significant escalation in the group’s tactics, specifically targeting networks that are physically separated from the internet for security, known as air-gapped networks.
Technical Details of the Attack Chain
According to the technical analysis, the attack begins with the deployment of a backdoor that uses Zoho WorkDrive, a legitimate cloud storage and collaboration platform, for its command and control infrastructure. This malware uses the service to fetch additional malicious payloads from attackers, effectively hiding its traffic within normal-looking cloud service communications.
Concurrently, the threat actors deploy a separate, sophisticated implant designed for removable media. This USB-focused malware is engineered to automatically execute when a compromised USB drive is inserted into a target computer within an air-gapped environment. It can then relay commands from the attackers and exfiltrate data back out when the USB device is reconnected to an internet-enabled system, bridging the air gap.
Attribution and Historical Context
The ScarCruft group, also tracked by other cybersecurity firms under names like APT37 and Reaper, is widely believed to operate on behalf of North Korea’s primary intelligence agency, the Reconnaissance General Bureau. The group has a long history of conducting cyber espionage campaigns targeting government, defense, and media organizations, primarily in South Korea but increasingly on a global scale.
This latest campaign showcases the group’s continuous innovation and adaptation. By leveraging a trusted cloud service for one stage of the attack and a USB-based method for another, they increase their chances of bypassing traditional network security defenses and reaching high-value, isolated targets.
Security Implications and Recommendations
The discovery of this campaign underscores the evolving challenges in cybersecurity, particularly for organizations managing sensitive, air-gapped networks. It highlights how threat actors are abusing legitimate cloud services to mask malicious activity and returning to physical media as a reliable intrusion vector for the most secure environments.
Security experts recommend that organizations enforce strict policies regarding the use of removable media, including disabling auto-run features on all systems. Monitoring for unusual network connections to cloud storage services, even those that are generally trusted, is also advised. For high-security environments, a defense-in-depth strategy combining technical controls, user training, and robust physical security protocols remains essential.
Zscaler has notified Zoho of the abuse of its WorkDrive platform in these attacks. The cloud service provider typically investigates and takes action to prevent the misuse of its services for malicious command and control. Cybersecurity agencies in multiple countries are expected to release advisories to their critical infrastructure sectors regarding this new threat methodology.
Source: Zscaler ThreatLabz