Security teams at Salesforce are alerting customers to a significant increase in malicious scanning activity targeting misconfigured public sites built on its Experience Cloud platform. The company stated that threat actors are using a modified version of an open-source security tool to find and exploit overly permissive guest user settings, potentially leading to unauthorized access to sensitive data.
The activity, which has been observed globally, does not exploit a vulnerability in Salesforce’s core software. Instead, it targets configuration errors made by customers when setting up public-facing Experience Cloud sites, formerly known as Community sites. These sites are often used for customer or partner portals.
Exploitation Method and Tool
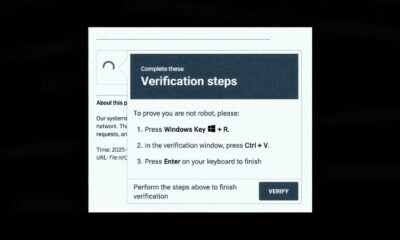
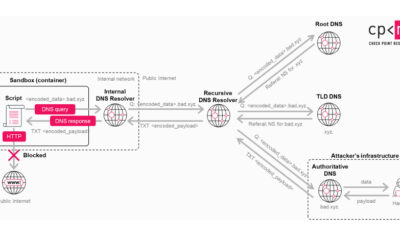
According to Salesforce’s security advisory, the attackers are employing a customized variant of a publicly available tool named AuraInspector. This tool is designed for security researchers to test the security posture of their own Experience Cloud implementations. The threat actors have adapted it to perform mass scans of the internet, identifying publicly accessible sites with lax security settings.
The primary weakness being exploited involves guest user profiles. When administrators configure an Experience Cloud site, they can grant access permissions to unauthenticated “guest” users. If these permissions are set too broadly, a guest user could view, modify, or extract sensitive organizational data that was not intended for public access.
Immediate Recommendations for Customers
Salesforce has urged all customers using Experience Cloud to immediately review their site configurations. The company emphasized verifying that guest user profiles are restricted to only the data and functions absolutely necessary for the public site’s purpose. Administrators should enforce the principle of least privilege.
The platform provider has published detailed guidance in its help documentation on how to properly secure guest user access. It recommends conducting a thorough audit of object, field, and page-level permissions assigned to guest profiles. Salesforce also advises reviewing any installed packages that may extend guest user privileges.
Broader Security Context
This wave of scanning attacks highlights a persistent challenge in cloud security: the shared responsibility model. While cloud providers like Salesforce are responsible for the security of the platform itself, customers are accountable for securing their own data and configurations within that platform. Misconfigurations remain a leading cause of data exposure.
Security experts note that the use of modified open-source tools by threat actors is a common tactic. Legitimate security and administration tools are frequently repurposed for malicious reconnaissance, making detection more challenging as the traffic can appear similar to normal administrative activity.
Salesforce has not attributed the scanning campaign to a specific threat group or nation-state actor. The company’s security teams are monitoring the situation and have implemented additional detection mechanisms on their infrastructure to identify attack patterns.
Next Steps and Ongoing Vigilance
Salesforce indicates that this type of opportunistic scanning is likely to continue as long as misconfigured sites remain accessible. The company expects to provide further updates to its security guidance as the threat landscape evolves. Customers are advised to treat configuration reviews as an ongoing process, not a one-time task, especially after making changes to their sites or installing new applications.
Source: Salesforce Security Advisory