A Russian national has been sentenced to two years in a U.S. federal prison for his role in managing a botnet used to deploy ransomware against American companies. The sentencing, announced by the U.S. Department of Justice, concludes a case highlighting international efforts to combat cybercrime originating from Russia.
Ilya Angelov, a 40-year-old from Tolyatti, Russia, received the prison term and was ordered to pay a $100,000 fine. Operating under the online aliases “milan” and “okart,” Angelov was identified as a co-manager of a cybercriminal group tracked by security researchers as TA551, also known as Shathak.
Operation of the TA551 Cybercrime Group
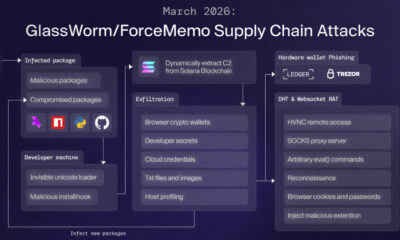
According to court documents, Angelov’s group operated a botnet, a network of compromised computers, to distribute malicious email campaigns. These emails were designed to trick recipients into opening attachments that would install malware, including notorious ransomware strains like IcedID, SystemBC, and Cobalt Strike.
The primary goal of these attacks was to encrypt the data of victim organizations and demand a ransom for its return. The group targeted a wide range of entities, with a particular focus on companies within the United States, causing significant financial disruption and operational damage.
Legal Proceedings and Guilty Plea
Angelov was apprehended in the Republic of Georgia in October 2022 and was subsequently extradited to the United States to face charges. He pleaded guilty to one count of conspiracy to commit computer fraud in a federal court in Connecticut.
In his plea, Angelov admitted to purchasing and configuring internet domains that were used as part of the botnet’s command-and-control infrastructure. This infrastructure was essential for sending instructions to the infected computers and managing the ransomware deployment campaigns.
Broader Context of Cyber Threats
The TA551 group has been active for several years and is considered a significant threat by cybersecurity firms. The group is known for its frequent shifts in tactics and for distributing multiple types of malware through large-scale email phishing operations.
This case is part of a wider pattern of cybercriminal activity with ties to Russia. U.S. authorities have repeatedly identified Russian-speaking cybercrime forums and groups as major sources of ransomware and other financially motivated cyber attacks targeting Western businesses and critical infrastructure.
Official Statements on the Sentencing
In a statement, a U.S. Attorney involved in the case emphasized that the sentence demonstrates the commitment of the Department of Justice to pursue cybercriminals regardless of where they are located. The official noted that holding individuals accountable for attacks on American networks is a top priority.
Law enforcement agencies, including the FBI, collaborated on the investigation. They highlighted the importance of international cooperation in apprehending suspects who operate across borders, using the technical and legal assistance of partner nations like Georgia.
The sentencing of Ilya Angelov is expected to be followed by continued investigations into other members and affiliates of the TA551 group. U.S. authorities have indicated that they will seek further extraditions and prosecutions related to this and similar cybercriminal networks. Analysts anticipate that such legal actions will persist as part of a long-term strategy to disrupt the economic models that make ransomware attacks profitable.
Source: U.S. Department of Justice