More News
-


Games
/ 7 days agoMobile Game Developed with AI for a Year Goes Unnoticed
A mobile game has reportedly been in development using artificial intelligence tools for approximately one year, a fact that remained undetected...
-


Games
/ 7 days agoNvidia DLSS 5 Announcement Sparks Sustained Industry Backlash
The Announcement of Nvidia‘s DLSS 5 technology earlier this week has been met with significant and ongoing criticism from segments of...
-

WordPress
/ 1 week agoWordPress.com AI Agents Gain Content Creation Capabilities
WordPress.com has expanded the functionality of AI agents connected to its platform, enabling them to create and manage website content directly....
-


Security
/ 1 week agoApple Warns Older iPhones Vulnerable to Exploit Kit Attacks
Apple has issued a security alert urging users of older iPhones to immediately update their device software. The warning addresses active...
-

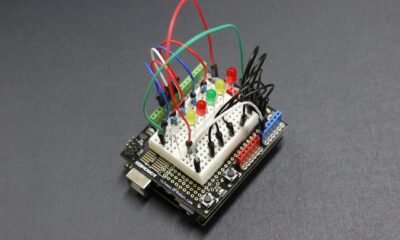
Security
/ 1 week agoU.S. DoJ Disrupts IoT Botnets Behind Massive DDoS Attacks
law enforcement agencies in the United States, Canada, and Germany have successfully disrupted the infrastructure of several major Internet of Things...
-


Security
/ 1 week agoCritical Magento Flaw Enables Unauthenticated RCE, Account Takeover
Security researchers have disclosed a critical vulnerability in the widely used Magento e-commerce platform that could allow attackers without any login...
-


Security
/ 1 week agoAI-Powered Cyberattacks Demand New Behavioral Defense Strategies
Security experts worldwide are reporting a significant evolution in the nature of cyber threats, driven by the adoption of artificial intelligence...
-


Security
/ 1 week agoGoogle Enforces 24-Hour Wait for Sideloading Unverified Android Apps
Google has instituted a mandatory 24-hour waiting period for users attempting to install Android applications from unverified developers outside of its...
-


Security
/ 1 week agoCritical Langflow Vulnerability Exploited Hours After Disclosure
A critical security vulnerability in the popular open-source framework Langflow is being actively exploited by attackers less than a day after...
-


Artificial Intelligence
/ 1 week agoEnergy Tech Emerges as Key Investment Amid AI Power Demands
The rapid expansion of artificial intelligence infrastructure is creating a significant bottleneck in global power supply, shifting investor attention toward the...
-

Tech News
/ 1 week agoDigital Greetings Rise for Eid Al-Fitr 2026 Celebrations
As Muslims worldwide prepare to mark the end of Ramadan in 2026, the exchange of digital greetings through images and animated...
-


Games
/ 1 week agoCD Projekt Sales Rise 9% in 2025 on Cyberpunk Strength
CD Projekt Group has reported a 9% year-on-year increase in sales revenue for the full fiscal year 2025, a result driven...
-


Mobile
/ 1 week agoLikewize, TMT First, Vodafone Win at Mobile News Awards 2026
Likewize, TMT First, and Vodafone Business were the major winners at the Mobile News Awards 2026, held at the London Hilton...
-

Security
/ 1 week ago54 EDR Killers Exploit 34 Signed Drivers to Bypass Security
A recent cybersecurity analysis has identified 54 distinct malicious tools, known as endpoint detection and response (EDR) killers, that are actively...
-


Security
/ 1 week agoSpeagle Malware Hijacks Cobra DocGuard to Steal Data
cybersecurity researchers have identified a new strain of malware, named Speagle, that is actively compromising systems worldwide. The malicious software operates...