Security researchers have identified a persistent and critical vulnerability in corporate cybersecurity defenses, where the implementation of multi-factor authentication (MFA) is failing to prevent widespread credential-based attacks. This issue is particularly prevalent in Windows enterprise environments globally, where attackers continue to compromise networks daily using stolen but valid login credentials. The problem stems not from a failure of MFA technology itself, but from significant gaps in its enforcement and coverage across an organization’s entire digital estate.
The Core of the Security Gap
Multi-factor authentication, a security standard that requires users to provide two or more verification factors to gain access to a resource, is widely mandated through corporate identity providers. These providers, such as Microsoft Entra ID, Okta, or similar platforms, are designed to act as gatekeepers. However, the security enforcement is only as strong as its implementation scope. Many applications, legacy systems, and service accounts within a network are often configured to bypass these centralized identity checks, creating what experts call “MFA blind spots.”
Attackers exploit these blind spots by using credentials obtained through phishing, data breaches, or other means. Because certain access paths do not require the second authentication factor, the stolen username and password alone become sufficient for unauthorized entry. This method of attack, known as credential abuse, remains one of the most common and effective vectors for network intrusion, even in organizations that consider themselves protected by MFA policies.
Technical and Operational Challenges
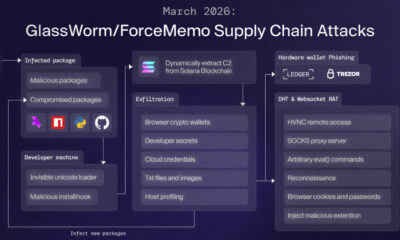
The challenge is twofold, involving both technical legacy and operational complexity. On the technical side, many older applications and on-premises servers were not designed to integrate with modern cloud-based identity providers. Forcing MFA on these systems can require costly and complex upgrades or replacement. Operationally, service accounts used for automated processes, such as database access or server-to-server communication, often cannot support interactive MFA prompts, leading administrators to exempt them from security policies.
Furthermore, inconsistent policy application across different departments and a lack of comprehensive asset inventory mean security teams may be unaware of all systems that fall outside MFA protection. This creates a fragmented security perimeter where robust protection at the main entrance, like a corporate VPN, is undermined by an unguarded side door, such as an outdated internal web portal.
Industry Response and Recommendations
In response to this ongoing threat, cybersecurity agencies, including the U.S. Cybersecurity and Infrastructure Security Agency (CISA), have repeatedly highlighted credential hardening as a top priority. Their guidance emphasizes that MFA must be applied uniformly to all access methods, especially for administrative and high-privilege accounts. Security firms recommend conducting regular audits to map all authentication pathways and identify systems that accept credentials without a second factor.
Additional recommended measures include implementing conditional access policies that evaluate risk based on user location, device health, and application sensitivity. The principle of least privilege, ensuring users and accounts have only the minimum access necessary, is also cited as a critical compensating control to limit the damage from any credential that is compromised.
Future Outlook for Identity Security
The industry is moving towards more seamless and comprehensive identity security models to address these gaps. The evolution towards passwordless authentication, which uses biometrics or security keys, aims to eliminate the primary credential theft vector altogether. Meanwhile, the adoption of Zero Trust architecture principles mandates that no user or device is trusted by default, requiring continuous verification for every access attempt, regardless of its origin within or outside the network perimeter.
Experts anticipate that regulatory frameworks and cyber insurance requirements will increasingly mandate proof of consistent MFA enforcement across all critical systems. Organizations are expected to accelerate the modernization of legacy applications and the implementation of unified identity management platforms to close the security gaps that currently enable credential-based attacks to succeed.
Source: Adapted from industry security analysis