A state-sponsored Iranian hacking group has launched a new cyber espionage campaign targeting organizations and individuals across the Middle East and North Africa. The activity, first detected on January 26, 2026, involves the deployment of previously unseen malware families designed for stealthy data theft.
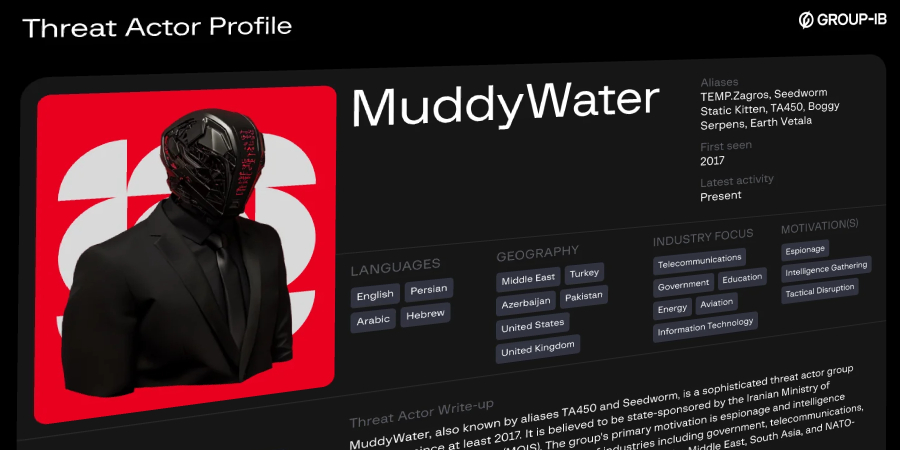
The threat actor, tracked as MuddyWater, is operating under the codename Operation Olalampo. Security researchers attribute the campaign to this group, which is also known by the aliases Earth Vetala, Mango Sandstorm, and MUDDYCOAST. The primary targets are located within the MENA region.
New Malware Arsenal Unveiled
The campaign is notable for its use of novel malicious tools. Analysts have identified three new malware families being deployed: GhostFetch, CHAR, and HTTP_VIP. These tools are engineered to avoid detection by standard security software and establish long-term access to compromised systems.
GhostFetch is a downloader designed to retrieve additional payloads from attacker-controlled servers. CHAR functions as a backdoor, providing remote control over infected machines. HTTP_VIP is a sophisticated tool used for covert communication, masking its network traffic to appear as legitimate web browsing activity.
Attribution and Historical Context
MuddyWater is widely believed to be an advanced persistent threat group with ties to Iran’s Ministry of Intelligence and Security. The group has been active since at least 2017, frequently targeting government agencies, telecommunications companies, and critical infrastructure in the Middle East and beyond.
Their tactics typically involve spear-phishing emails containing malicious documents. Once a user opens the document, it executes code that downloads the group’s malware. This latest campaign follows established patterns but showcases an evolution in their technical capabilities with the new tools.
Implications for Regional Security
The targeting of MENA organizations highlights ongoing cyber tensions in the region. Cyber espionage campaigns are often used to gather intelligence, steal sensitive information, and maintain strategic awareness. The deployment of new malware suggests the group is actively working to bypass improved security measures implemented by potential targets.
Security firms monitoring the group have not disclosed the identities of the specific organizations compromised in Operation Olalampo. The broad targeting, however, indicates a wide-ranging intelligence collection effort rather than a focused attack on a single entity.
Recommended Defensive Measures
Cybersecurity experts recommend several steps for organizations, particularly those in the MENA region, to defend against such threats. These include implementing robust email filtering to block phishing attempts, applying security patches promptly, and using endpoint detection and response tools. User awareness training to identify suspicious emails remains a critical first line of defense.
Network monitoring for unusual outbound traffic, especially to unknown servers, can help identify infections from tools like HTTP_VIP. Security teams are advised to review indicators of compromise associated with the new malware families and update their detection systems accordingly.
Based on the group’s historical behavior, MuddyWater’s Operation Olalampo is expected to continue in the coming weeks. Security analysts anticipate further technical analysis of the new malware will be published, providing deeper insight into its functionality. Affected organizations are likely to work with national cybersecurity authorities to mitigate the threats and investigate the full scope of the breaches.
Source: GeekWire